If a strange email about a “payment detail request” or “signed bank document” lands in your inbox, your best bet is to delete it immediately. A fresh investigation by Fortinet’s FortiGuard Labs warns that scammers are using these mundane business themes to infect Windows PCs with XWorm malware.
XWorm is a Remote Access Trojan (RAT), which is a tool capable of giving a hacker full remote control of compromised Windows systems. While the virus has been around since 2022, this latest version (XWorm 7.2) is a much more advanced breed that surfaced on Telegram marketplaces as recently as late 2025 and early 2026.
How the Trap is Set
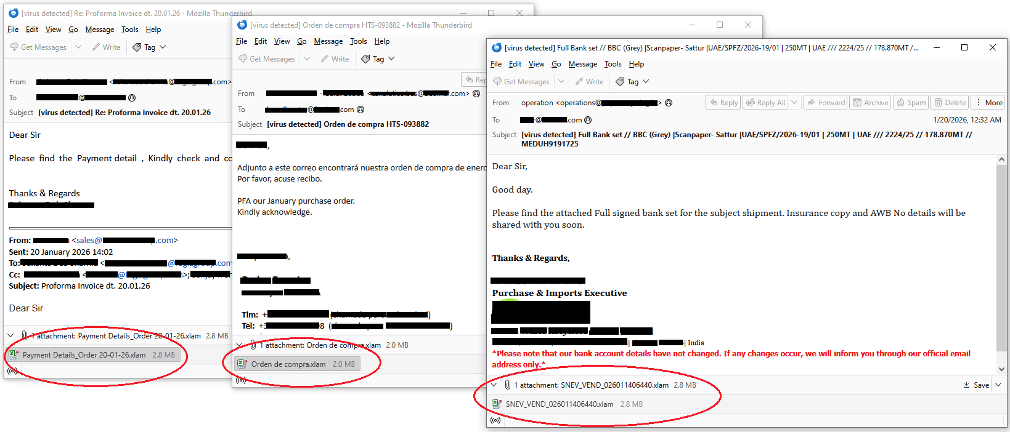
As we know it, attackers rely on social engineering to make a fake email feel urgent. Researchers found multiple email themes written in different languages. Mostly these lure emails were disguised as:
- General business queries.
- Payment reviews or purchase orders.
- Signed bank documents for shipments.
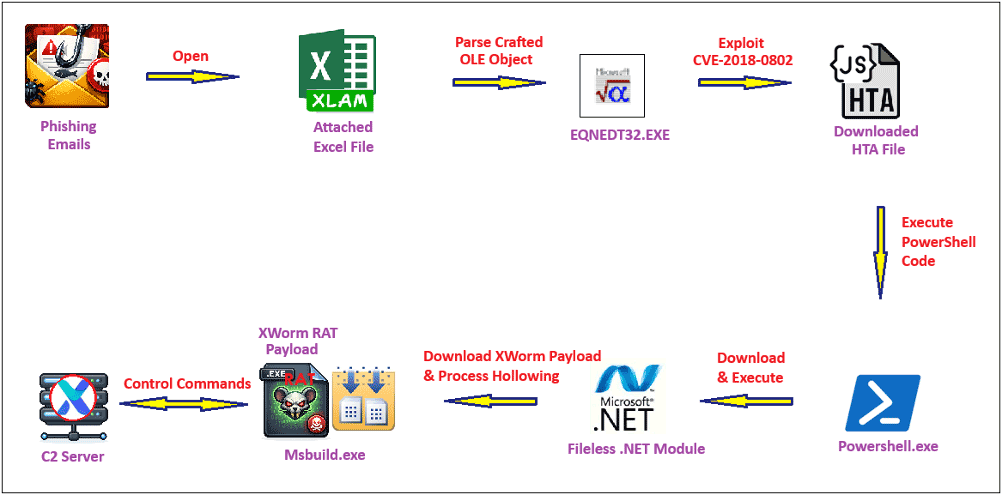
These emails usually come with an Excel attachment; when opened, the file exploits an old security vulnerability tracked as CVE-2018-0802. This triggers a domino effect, running a hidden script (an HTA file) which uses PowerShell to download what looks like a normal JPEG photo. However, tucked inside that image, between markers labelled BaseStart and BaseEnd, is the actual malware.
The Invisible Infection
The most worrying part of this campaign is a trick called process hollowing. According to researchers, the malware starts a legitimate Windows program (Msbuild.exe) but immediately pauses it and erases its internal code. It then replaces that code with the XWorm virus.
To your antivirus software, it looks like a trusted system tool is running, but in reality, a hacker is now in the driving seat. The malware then connects to a control server at berlin101.com using port 6000 and AES encryption to lock up and hide any data it steals.
Why XWorm is Dangerous
FortiGuard researchers explain in the blog post that XWorm is highly dangerous because it uses a modular setup, so hackers can add over 50 different plugins to expand its reach. Currently, it can steal everything from Wi-Fi keys and passwords to browser cookies. It can even spy on you via your webcam or log every single key you press.
Furthermore, the malware even has built-in features for ransomware and launching DDoS attacks to crash websites. Researchers noted that since XWorm “hides so well in the system registry,” it is incredibly difficult to remove once it takes hold. The best defence remains keeping your software updated and staying cautious of unexpected attachments.
Experts Insights:
Sharing their thoughts with Hackread.com, industry experts suggest that the danger lies in how well these old tricks are put together.
Shane Barney, Chief Information Security Officerat Keeper Security, noted that while the techniques aren’t brand new, they are effective. “This campaign is striking in its ordinariness. There’s no breakthrough technique here,” Barney said. “It’s a clean execution chain built from components we’ve all seen before. The sophistication isn’t in the novelty. It’s in the assembly.” He warned that because XWorm is sold openly, “enterprise-grade intrusion capability” is now available to almost anyone.
Jason Soroko, Senior Fellow at Sectigo, pointed out that the hackers are confident that “legacy Office exploit paths still convert at scale.” Soroko explained that the choice to hide inside Msbuild.exe is a deliberate move to “blend in” by using a legitimate Windows file. According to Soroko, XWorm has become so advanced that simply calling it a “RAT” might be an understatement. “AES-encrypted C2 packets and a broad plugin ecosystem push XWorm firmly into a mature, modular platform category where ‘RAT’ understates the risk,” he noted.