North Korean cyber operations are moving into the commercial ransomware market, pointing to a stronger focus on generating direct financial gains. Recent evidence from the Symantec and Carbon Black Threat Hunter Team shows the notorious state-backed Lazarus Group has been deploying Medusa ransomware against targets in the Middle East and attempting to breach healthcare organizations in the United States.
While the US attempt failed, the incident confirms that state-sponsored actors are increasingly utilizing established cybercrime tools to bypass traditional protection.
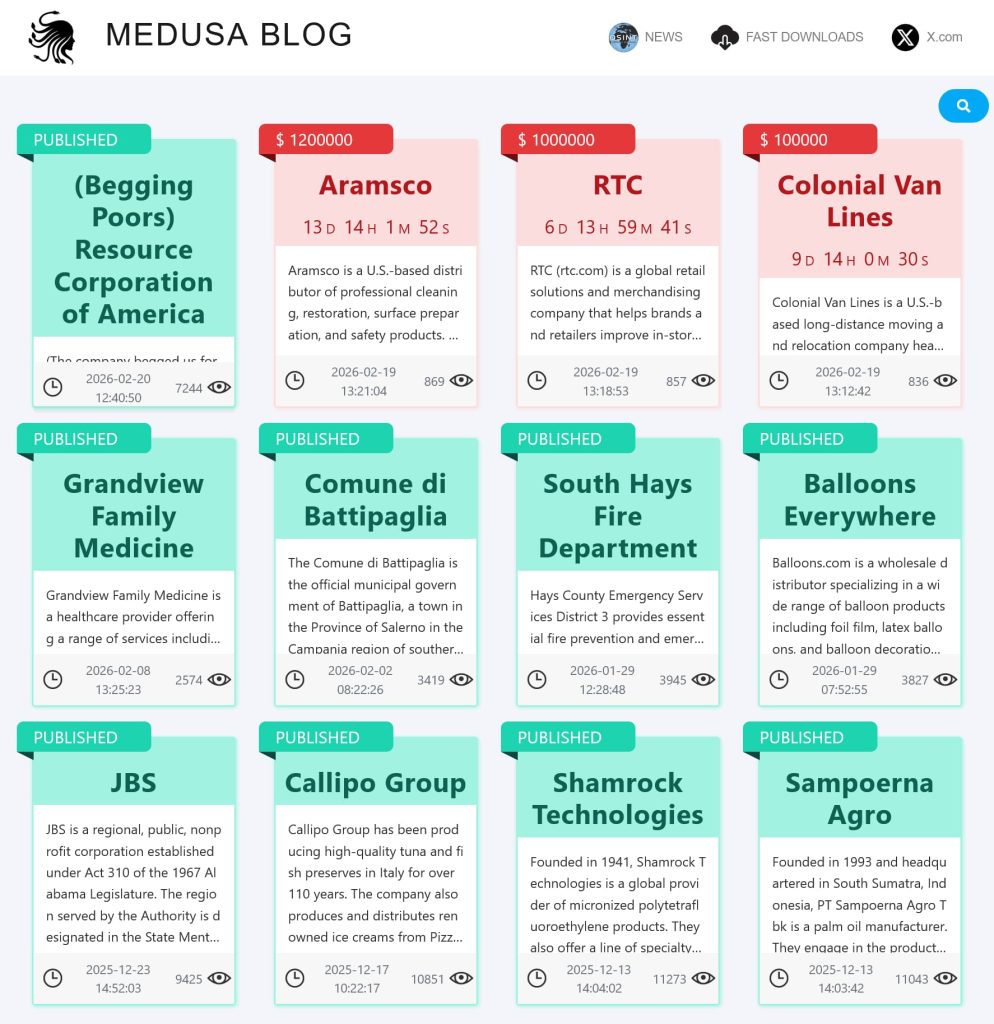
For your information, the Medusa ransomware operates as a service where affiliates use the software to lock down networks and demand payments in exchange for a cut of the profit. Since its arrival in 2023, the group behind the code has been linked to over 300 successful attacks, including Comcast and NASCAR.
Now, by joining hands with Medusa, Lazarus has gained access to an existing infrastructure that hides their identity behind the persona of a common cyber criminal gang, making attribution and defense more difficult for cybersecurity researchers and law enforcement authorities.
Multi-Stage Attack Chain
According to Symantec’s blog post shared with Hackread.com, the Lazarus group’s attacks follow a multi-stage process with Medusa ransomware deployed only at the very end. Long before encryption begins, the group deploys a specialized toolkit to dismantle local security protection.
They then move onto the next step, including installing custom backdoors and trojans, including Blindingcan and Comebacker, giving them lasting access to compromised networks. The next step is to deploy credential theft tools such as ChromeStealer and Mimikatz to collect passwords, while a tool known as Infohook scans for and stages sensitive data for exfiltration.
To move stolen information without drawing notice, the group uses RP_Proxy to route traffic internally and relies on the command-line utility Curl to send files back to its own servers. By the time the Medusa ransomware is finally launched, the attackers already have full control of the network and have extracted its most valuable data.
Targets: Vulnerable Institutions
Targeting patterns, as per researchers, reveal a specific focus on organizations that provide essential social services. In the last few months, the Medusa leak site has named several US victims, including a mental health non-profit and a school that supports children with autism.
These attacks often come with a financial demand averaging around $260,000, a figure calculated to be high enough for a significant payday but low enough that a desperate organization might consider paying to restore services.
Not The First Time
This is not the first time that a state-backed North Korea threat actor group has joined hands with a ransomware group. In October 2024, as reported by Hackread.com, Jumpy Pisces, also known as Onyx Sleet and Andariel (also known as the “Guardians of Peace” APT, which was behind the infamous HBO data breach), collaborated with the Play ransomware group to carry out cyberattacks.
The collaboration was spotted by Palo Alto Networks Unit 42, who noted that the hackers were utilizing tools such as the open-source Sliver and their custom DTrack malware to move laterally and maintain persistence across the network.
Expert View
Jason Soroko, Senior Fellow at Sectigo, a Scottsdale, Arizona-based provider of comprehensive certificate lifecycle management (CLM), notes the cold logic behind these choices.
“Striking facilities dedicated to mental health and autistic children demonstrate that these actors prioritize maximum emotional leverage to ensure swift ransom payments. The relatively modest average ransom demand suggests a volume-based approach where threat actors target chronically underfunded sectors that simply cannot afford prolonged operational downtime,“ Soroko noted.
This trend suggests that the divide between state-sponsored espionage and street-level extortion is disappearing. When a group like Lazarus adopts Medusa, they bring the resources of a national government to bear against small, local institutions.
Organizations that previously felt they were too small to be a target for international hackers now find themselves at the center of global cyber warfare, requiring a rethink of how smaller non-profits and clinics protect their sensitive data.