A new Android malware called Oblivion is turning everyday Android smartphones into open books for cybercriminals who are willing to pay a $300 (roughly £230) monthly subscription. What’s worse, this Remote Access Trojan (RAT) is being sold openly on the public web rather than the dark web.
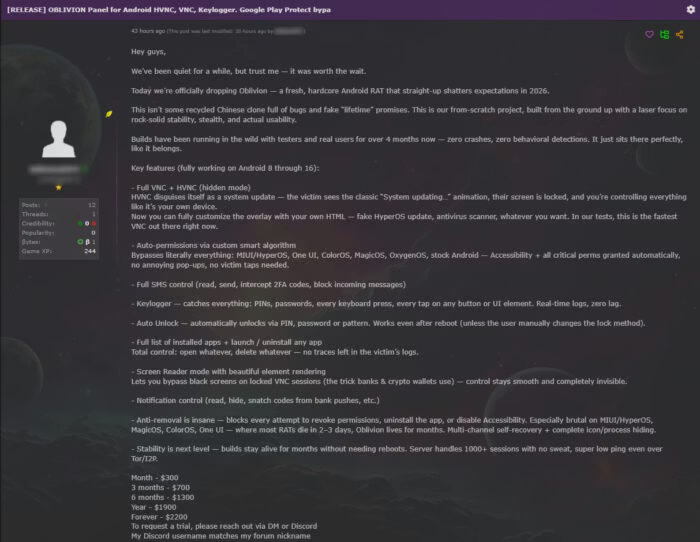
The research was conducted by the security firm Certo and shared with Hackread.com. Their team found that the software is specifically designed to be easy to use, which means a person does not need to be a computer expert to spy on others. For those looking for long-term access, the hackers even offer a lifetime access deal for $2,200, and other options like $700 for three months or $1,300 for six months.
How the Attack Works
While most smartphone malware rely on users clicking through confusing pop-ups, Certo researchers found that Oblivion is much sneakier. It usually arrives via a fake Google Play update message. Once a user triggers this “update,” the malware silently grants itself full permissions, including the powerful Accessibility Service, without the owner ever touching the screen. This feature, designed for disabled users, basically acts as a master key for hackers.
Further probing revealed that once inside, the software can read private SMS messages to steal bank codes and use a keylogger to capture every password and PIN you type. It can even remotely unlock your phone after a restart.
Most concerningly, hackers can watch your screen live using a hidden mode; while you see a fake “system updating” animation, the attacker is busy navigating your apps in the background. The system is built for scale; researchers noted in the blog post that the infrastructure can handle over 1,000 victims simultaneously, even when using the Tor network to remain anonymous. Researchers noted that Oblivion is a “genuine step-change” because it is “built from the ground up to be harder to stop.”
Major Brands at Risk
According to researchers, Oblivion is not just a threat to old phones; it works on almost every modern Android version, from Android 8 to the upcoming Android 16. It is designed to bypass the custom security layers used by major brands, specifically naming the following:
- HyperOS
- Xiaomi’s MIUI
- OPPO’s ColorOS
- Honor’s MagicOS
- Samsung’s One UI
- OnePlus’s OxygenOS.
The seller claims the malware was tested for 4 months before release to ensure it has no behavioural detections and remains hidden from antivirus software. It even includes an APK Builder that lets hackers create a fake app, like Google Services, in just a few clicks.
Certo researchers conclude that the infection works because it looks like a routine part of using a phone, so staying cautious about where you download apps is your best defence. If your phone suddenly stays stuck on an update screen you did not start, turn the device off immediately and run a security scan.