Online scams usually involve fake websites with names that look slightly off, but a new investigation has found that threat actors are now leveraging the .arpa top-level domain (TLD), a reserved segment of the internet’s infrastructure, to bypass standard security protocols.
Infoblox, a DNS security and management firm, recently discovered these campaigns abusing a space that was never intended to host web content. Unlike common endings like .com or .net, which are meant for hosting websites, .arpa is a reserved space used strictly for internet infrastructure. It is primarily used for reverse DNS, a process that maps an IP address back to a domain name.
Exploiting IPv6 Tunnels and Reverse DNS
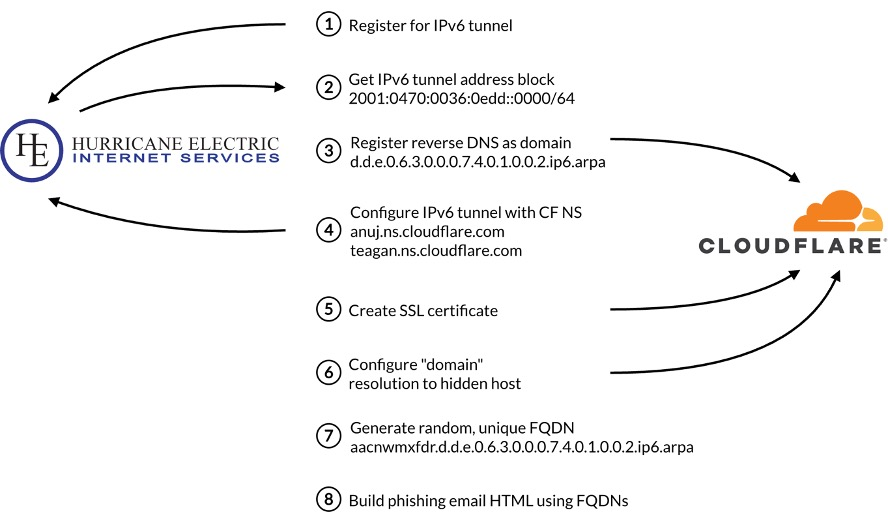
According to researchers at Infoblox Threat Intel, the scammers use free services called IPv6 tunnels to get a massive supply of IP addresses. They then trick certain service providers into letting them host fraudulent websites inside the .arpa space. They specifically used providers like Hurricane Electric and Cloudflare to create these records.
Because this area of the internet is considered essential and trusted for network operations, many security tools do not even think to check it for threats. Dr. Renée Burton, VP Infoblox Threat Intel, noted that by using .arpa, these actors “effectively step around traditional controls” that usually flag suspicious links.
“Reverse DNS space was never designed to host web content, so most defenses don’t even look at it as a potential threat surface. By turning .arpa into a delivery mechanism for phishing, these actors effectively step around traditional controls that depend on domain reputation or URL structure. Defenders need to start treating DNS infrastructure itself as high-value real estate for attackers, and they need the visibility to see abuse in any type of location.”
More Than Just One Trick
It is worth noting that the .arpa abuse is just one part of the story. Researchers noted in the blog post, shared exclusively with Hackread.com, that the group also uses dangling CNAMEs, essentially taking over old, forgotten web links from organisations. This includes universities, media companies, and even government agencies.
In one case, a domain called publicnoticessitescom expired, allowing the scammers to hijack over 120 local newspaper websites at once. Another expired domain, hobsonsmscom, allowed them to target at least three different universities.
They also use a tactic called domain shadowing, where they create a secret subdomain under a legitimate brand’s name, generally through stolen login details. One such shadow domain has reportedly operated since 2020 without being caught.
Spotting the “Free Gift” Trap
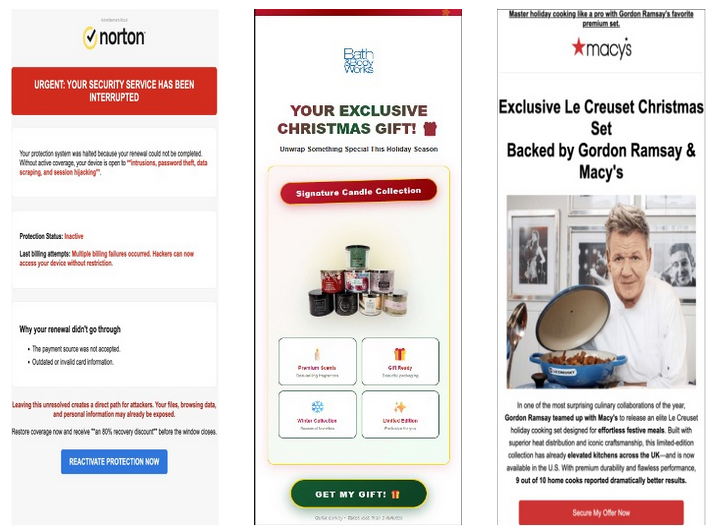
The actual emails sent to victims are simple, typically promising a gift or claiming a cloud storage quota has been exceeded. Instead of text, the email is usually just one large image, and clicking the image sends the user through a Traffic Distribution System (TDS), which checks if the victim is on a mobile device or using a residential IP address before showing the final scam page.
These lures, as we know them, are designed to steal credit card details under the guise of paying for shipping. To protect yourself, always be wary of too good to be true offers, especially those that arrive as clickable images from unknown sources.