The University of Hawaii (UH) has confirmed that a major security breach at its Cancer Centre has significantly affected more people than first thought, with the total now reaching approximately 1.24 million individuals. The incident, which was first detected on 31 August 2025, involved a ransomware attack that targeted the centre’s research systems.
The university stated that the attack specifically hit servers belonging to its Epidemiology Division, and officials have been clear that this incident did not impact clinical operations, patient care, or student records.
Why was so much data taken?
The university’s official notice revealed that the breach involved two main groups of people. The first includes about 1.15 million individuals whose personal details were found in historical records. These records were collected in 1998 and 2000 from voter registration and the Department of Transportation.
It is worth noting that during the 1990s, it was common practice for Hawaii government agencies to provide these lists to the university. Because Social Security numbers (SSNs) were often used as primary identifiers back then, they were unfortunately included in these old recruitment files.
The second group includes 87,493 participants of the long-running Multiethnic Cohort (MEC) Study, which started in 1993, and followed residents from Hawaii and Los Angeles, California. According to the university, the stolen files for this group included names, addresses, SSNs, and in some cases, health-related information.
The decision to pay the ransom
While the 27 February public notice mentions that the university “engaged” with the yet unidentified threat actors, earlier reports confirm that the university made the “difficult decision” to pay a ransom. This was done to obtain a decryption tool to unlock their systems and to secure a promise that the stolen data was destroyed.
“The UH Cancer Centre deeply regrets that this incident occurred,” said Director Naoto T. Ueno in the latest notice. He stated that the centre is now focused on “transparency, accountability and strengthening protections” for the data it holds.
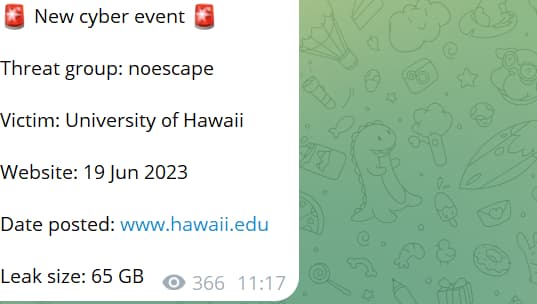
However, this is not the first ransomware incident involving the University of Hawaii. In June 2023, the NoEscape ransomware group claimed a breach at the university and said it stole 65GB of sensitive data.
If you are concerned your details were involved, the university is offering 12 months of free credit monitoring and $1 million in identity theft insurance. A dedicated call centre at (844) 443-0842 is now open to help people check their status. It is important to act quickly, as the deadline to sign up for these free services is 31 May 2026.
Experts’ Perspectives
Several cybersecurity experts shared their views on the incident with Hackread.com, providing context on why these attacks are so difficult to manage.
John Bambenek, President at Bambenek Consulting, raised concerns about the long delay in notifying the public. He pointed out that many laws do not require a notice if the data is encrypted, but in this case, “the attacker likely had their hands on enough data to engage in identity or credit fraud for six months” while the victims were unaware.
“Many breach notification laws include a “safe harbor” provision that notification isn’t necessary if the attacker couldn’t access the underlying data due to encryption. That means the attacker likely had their hands on enough data to engage in identity or credit fraud for six months when the affected individuals could have had credit monitoring or freezes put in place to protect themselves.”
Jason Soroko, Senior Fellow at Sectigo, explained that when hackers aggressively lock up data and indexing systems, the process of finding out what was stolen “becomes complex.” He noted that:
“Security teams must enforce aggressive network segmentation and deploy immutable, offline backups that cannot be easily reached by automated ransomware strains. Stronger forms of authentication are analogous to putting stronger locks on the doors to make lateral movement more difficult. With certificate-based authentication, along with automated certificate lifecycle management, organizations can revoke compromised credentials, identify anomalous encrypted traffic, and significantly shrink the window of opportunity a ransomware operator has to map the network and achieve their goals.”
Finally, Guru Gurushankar from ColorTokens noted that these types of attacks on the healthcare and research industry are not slowing down. He argued that it is now “essential to survival” for organisations to stop hackers from moving through their internal networks. He concluded that “organizations have to become breach-ready” to maintain their resilience against these relentless threats.
“Throughout the past year, we have seen healthcare industry breaches which highlight the necessity of preventing unauthorized lateral movement within one’s network. This is critical for healthcare organizations to maintain their digital operational resilience in the face of relentless cyberattacks, and it does not appear that there will be any letup from these attacks moving forward. In other words, organizations have to become breach-ready – this is essential to survival.”