A Pakistan-based hacking group is flooding Indian government networks with a new breed of disposable malware, marking a strange shift in the digital conflict between the two nations. This isn’t a story of high-tech genius, but rather a move toward what researchers at Bitdefender call Vibeware- a wave of mediocre, AI-generated code designed to overwhelm security systems by sheer volume.
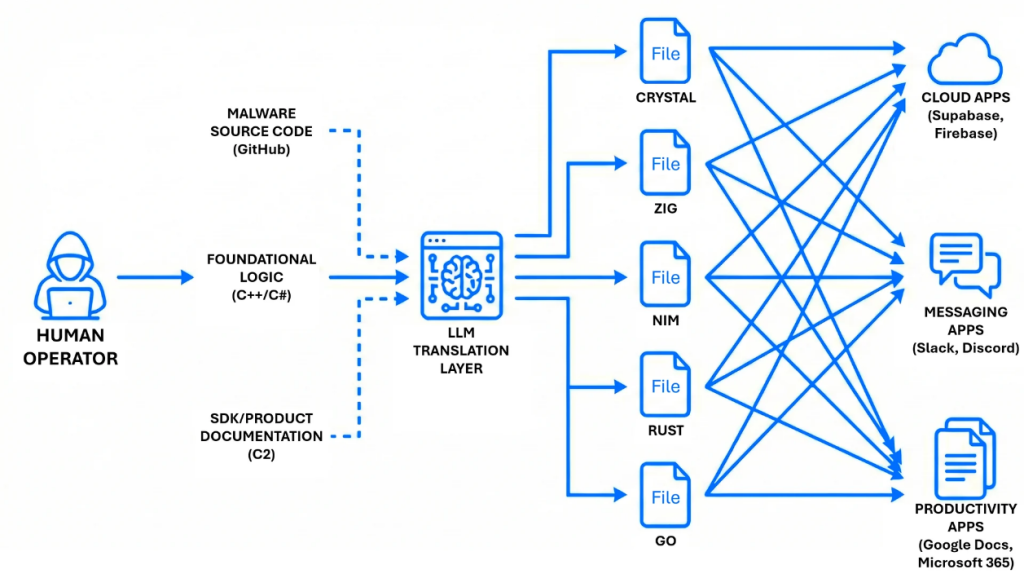
According to Bitdefender’s latest research, shared exclusively with Hackread.com, the group behind the attacks, APT36 (or Transparent Tribe), has shifted from standard tools and is now using AI to rapidly develop software in niche programming languages like Nim, Zig, and Crystal to evade traditional antivirus scanners.
The Kumar Game and Sloppy Mistakes
It is worth noting that while production is fast, the quality is often extremely low. In one case, the hackers deployed a tool meant to steal browser data but forgot to include the web address to send the info to, so, basically, the tool was phoning home to nowhere.
Further probing revealed a calculated psychological game. Researchers found a common Hindu name, “Kumar,” hidden inside the code’s file paths, suggesting the developers are planting digital crumbs to trick investigators into looking for a culprit within India. They even named a Discord server “Jinwoo’s Server,” a nod to a popular anime, to blend in with regular internet culture.
Picking Browser Locks and Desktop Traps
Despite the errors, some tools are genuinely intrusive. A tool called LuminousCookies was caught red-handed trying to bypass App-Bound Encryption, a security lock used by Chrome and Edge to protect your saved passwords. What’s most intriguing is that instead of cracking the lock from the outside, the malware forces itself into the browser’s own memory, pretending to be a legitimate part of the program to get the keys.
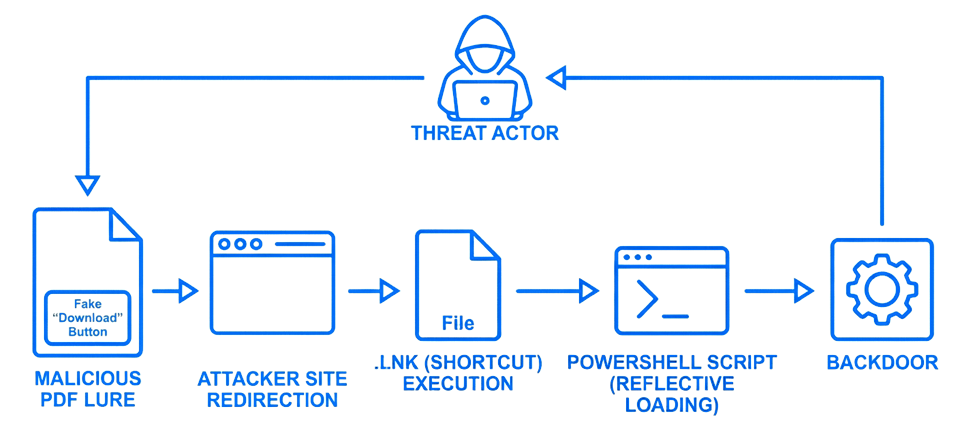
We usually trust our desktop icons, but APT36 is exploiting this trust by modifying shortcuts for Google Chrome and Microsoft Edge. When an official clicks their browser, they silently launch a background spy. This often starts with a fake resume PDF that tricks users into clicking a “Download” button that installs the virus.
Digital Dragnets and Cloud Hiding
For your information, the group is also living inside work services. They use Google Sheets for instructions and Slack or Discord to send out stolen files. By using these platforms, their malicious activity looks like a regular office worker updating a spreadsheet.
Once inside, they deploy watchers like BackupSpy. This tool acts as a digital dragnet, scanning every drive and USB stick for a specific list of 16 file types, including Office documents (.docx, .xlsx) and PDFs to images (.png, .jpg), and even web files (.html). It even keeps a manifest or inventory list to track exactly what has been stolen.
Researchers noted this malware-a-day strategy targeting the Indian government and its diplomatic missions. They aren’t trying to build a master key; they are throwing thousands of cheap, AI-made keys at the door, hoping one will eventually turn. It is a Distributed Denial of Detection where the goal is to simply exhaust the defenders.
In the end, the campaign shows that APT36 is leaning on quantity over quality. Instead of building a few sophisticated tools, the group appears to be pushing out large numbers of AI-assisted malware samples and seeing what gets through.
Many of these programs are sloppy and sometimes even broken, but the constant stream of new variants increases the chance that at least a few will bypass security defenses. For security teams, that means dealing with a steady flood of low-grade threats while still trying to catch the handful that actually work.