For many online gamers, the temptation to get a competitive edge in hits like Fortnite or Counter-Strike is high. However, a new wave of cyberattacks is proving that ‘free’ cheats often come with a heavy price tag. Cybersecurity experts at the research firm Acronis TRU have identified a huge campaign using platforms like GitHub and Reddit to spread a dangerous infostealer called Vidar 2.0.
How the Scam Works
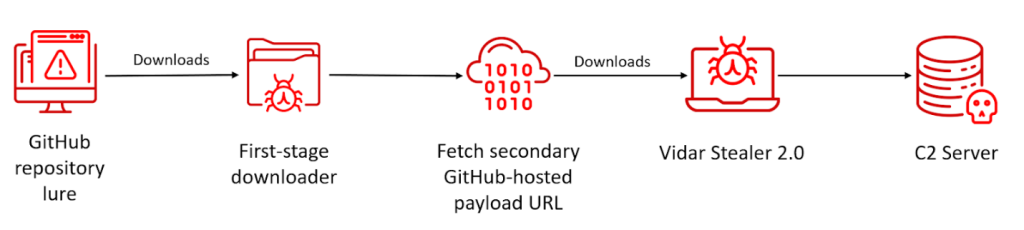
In this campaign, hackers hide malicious links behind professionally designed images on GitHub and use Discord or Reddit to identify victims. These cheats typically ask users to disable their antivirus software to function. This is the perfect trap, because cheats naturally behave like viruses to bypass game security, and victims ignore the warnings and hand over total control of their PCs.
This campaign specifically targets younger players who may not have the money for paid subscriptions, as they often ignore safety warnings and are too embarrassed to report the hack since they were trying to cheat.
According to researchers, the scam’s scale is likely underestimated; while they found hundreds of malicious pages, the true number could be in the thousands. They also noted that hackers use technical tricks like PowerShell scripts to drop the virus quietly. It even sets itself up to run every time a user logs in and will refuse to run if it detects a security researcher’s virtual environment.
Vidar 2.0: A Master of Digital Theft
This research, which was shared exclusively with Hackread.com, shows that Vidar 2.0 has undergone a complete technical rewrite. Changing its code from C++ to C has made it much faster and stealthier. Interestingly, Vidar has been around since 2018, but it is seeing a surge now following the recent shutdown of its main rivals, Lumma and Rhadamanthys. For your information, Vidar operates as Malware-as-a-Service (MaaS), where criminals pay between $130 and $750 to use it.
The virus is much more dangerous than older versions, targeting everything from Monero cryptocurrency wallets to login tokens for Discord, Steam, and Telegram. It even hunts for Microsoft Azure folders and professional tools like FileZilla to steal server passwords, potentially giving hackers access to a victim’s workplace networks. To make things more personal, it takes a screenshot.jpg of the user’s desktop and copies files from the Documents and Downloads folders.
Researchers further explain that to avoid being caught, the virus uses Telegram bots and Steam profiles as “dead drop” locations to receive hidden instructions. By blending in with normal traffic from these popular apps, the malware often “completes its mission” before the victim even realizes something is wrong. This makes it all the more important for you to download software only from trusted, official sources and avoid the lure of free advantages.