
Threat actors are targeting TikTok for Business accounts in a phishing campaign that prevents security bots from analyzing malicious pages.
TikTok Business accounts may be targeted due to their high potential for abuse in malvertising campaigns, ad fraud, and the distribution of malicious content.
Browser threat detection and response company Push Security links the campaign to one documented last year, which targeted Google Ad Manager accounts.
TikTok has previously been used to spread information-stealing malware via malicious videos, as well as cryptocurrency scams via fake promotions. TikTok for Business accounts are ideal for such purposes due to their increased reach and perceived legitimacy.
In a report shared with BleepingComputer, Push Security says that victims are lured to Cloudflare-hosted phishing pages registered on March 24 via NiceNIC, a registrar often reported by cybersecurity researcher for being used for cybercriminal activities.
Push Security could not determine the initial delivery mechanism, but believes that the threat actor uses a similar method as observed in activity reported by Sublime Security.
The initial link redirects via a legitimate Google Storage URL, blocks bots using a Cloudflare Turnstile check, and then redirects to the malicious pages.
The domains feature similar names, and are all hosted on the same Google Storage bucket:
- welcome.careerscrews[.]com
- welcome.careerstaffer[.]com
- welcome.careersworkflow[.]com
- welcome.careerstransform[.]com
- welcome.careersupskill[.]com
- welcome.careerssuccess[.]com
- welcome.careersstaffgrid[.]com
- welcome.careersprogress[.]com
- welcome.careersgrower[.]com
- welcome.careersengage[.]com
- welcome.careerscrews[.]com
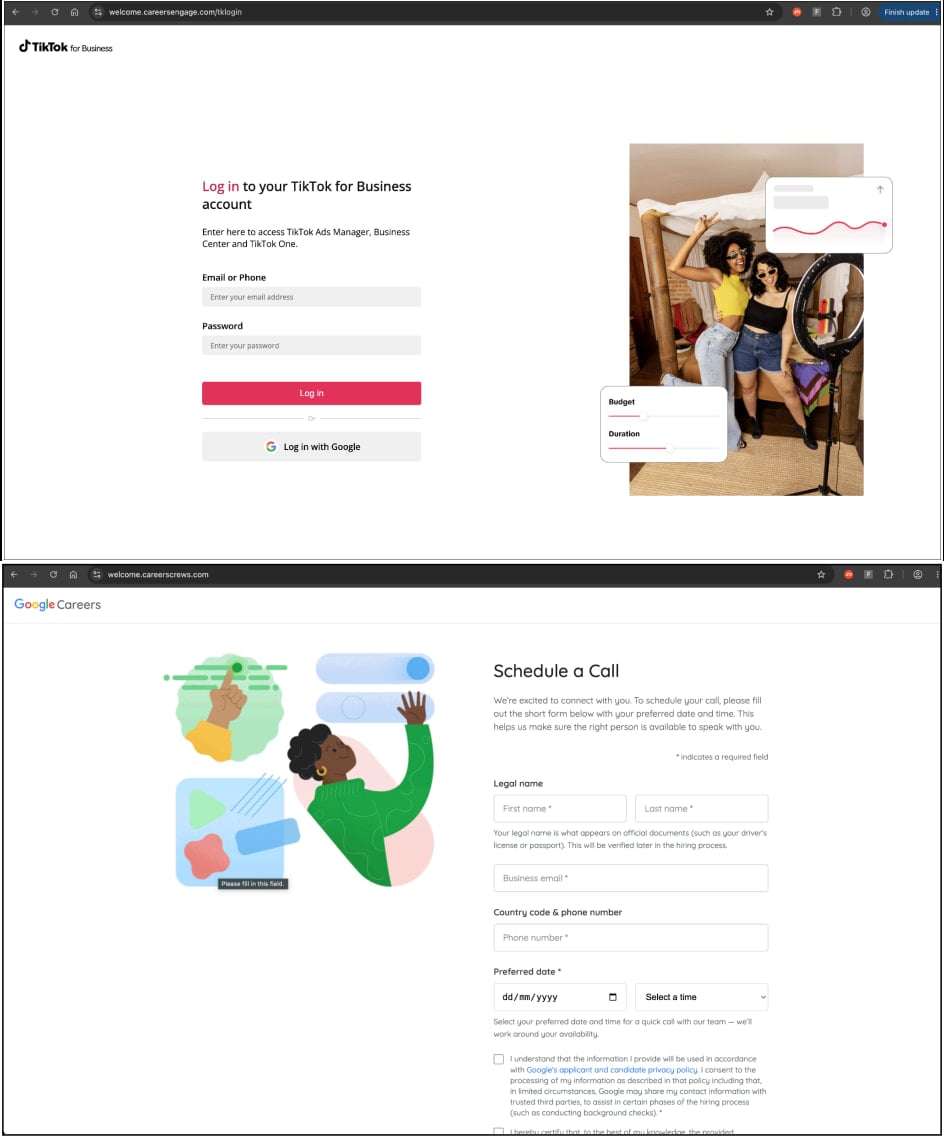
The malicious pages impersonate TikTok for Business and Google Careers “Schedule a Call” pages, requesting visitors to enter basic information in a form to validate they’re using a business email address.
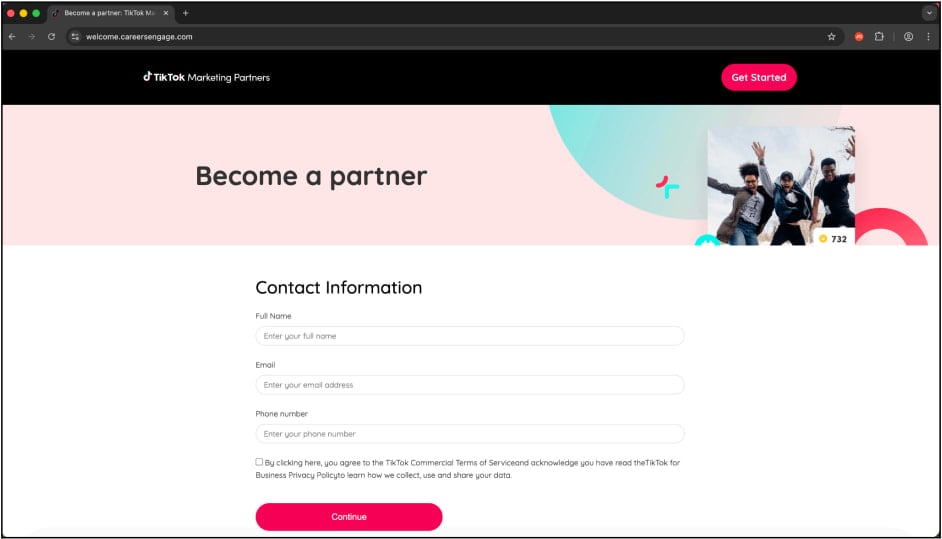
Source: Push Security
After this step, victims are served a fake login page, which is a reverse proxy designed to capture credentials and session cookies, and to exfiltrate them to the attacker.
Since the page acts as an intermediary between the legitimate user and the service, the threat actor can hijack accounts even when the two-factor authentication (2FA) protection is active.
Source: Push Security
Push Security also notes that business account holders often log into TikTok via Google single sign-on (SSO) service. “This means that anyone using Google to login to their TikTok account will effectively have both accounts used to distribute ads compromised in one go.”
Users should be extremely cautious with suspicious invites and job offers, and never trust links sent from unknown contacts. Always check the domain before entering credentials, and use passkeys to protect valuable accounts.
Red Report 2026: Why Ransomware Encryption Dropped 38%
Malware is getting smarter. The Red Report 2026 reveals how new threats use math to detect sandboxes and hide in plain sight.
Download our analysis of 1.1 million malicious samples to uncover the top 10 techniques and see if your security stack is blinded.
Related Articles:
Dutch govt warns of Signal, WhatsApp account hijacking attacks
Phishing campaign targets freight and logistics orgs in the US, Europe
Hackers target Microsoft Entra accounts in device code vishing attacks
Germany warns of Signal account hijacking targeting senior figures
Bubble AI app builder abused to steal Microsoft account credentials
