
The maintainers of the popular Axios HTTP client have published a detailed post-mortem describing how one of its developers was targeted by a social engineering campaign linked to North Korean hackers.
This follows the threat actors compromising a maintainer account to publish two malicious versions of Axios (1.14.1 and 0.30.4) to the npm package registry, triggering a supply chain attack.
These releases injected a dependency named plain-crypto-js that installed a remote access trojan (RAT) on macOS, Windows, and Linux systems.
The malicious versions were available for roughly three hours before being removed, but systems that installed them during that period should be considered compromised, and all credentials and authentication keys should be rotated.
The Axios maintainers said they have wiped affected systems, reset all credentials, and are implementing changes to prevent similar incidents.
The Google Threat Intelligence Group has since linked this attack to North Korean threat actors tracked as UNC1069.
“GTIG attributes this activity to UNC1069, a financially motivated North Korea-nexus threat actor active since at least 2018, based on the use of WAVESHAPER.V2, an updated version of WAVESHAPER previously used by this threat actor,” explains Google.
“Further, analysis of infrastructure artifacts used in this attack shows overlaps with infrastructure used by UNC1069 in past activities.”
Targeted in a social engineering attack
According to a post-mortem, the compromise began weeks earlier through a targeted social engineering attack on the project’s lead maintainer, Jason Saayman.
The attackers impersonated a legitimate company, cloned its branding and founders’ likenesses, and invited the maintainer into a Slack workspace designed to impersonate the company. Saayman says the Slack server contained realistic channels, with staged activity and fake profiles that posed as employees and other open-source maintainers.
“They then invited me to a real slack workspace. this workspace was branded to the companies ci and named in a plausible manner,” explained Saayman in a post to the post-mortem.
“The slack was thought out very well, they had channels where they were sharing linked-in posts, the linked in posts i presume just went to the real companys account but it was super convincing etc. they even had what i presume were fake profiles of the team of the company but also number of other oss maintainers.”
The attackers then scheduled a meeting on Microsoft Teams that appeared to include numerous people.
During the call, a technical error was displayed, claiming that something on the system was out of date, prompting the maintainer to install a Teams update to fix the error. However, this fake update was actually RAT malware that gave threat actors remote access to the maintainer’s device, allowing them to obtain the npm credentials for the Axios project.
Other maintainers reported similar social engineering attacks, where the threat actors tried to get them to install a fake Microsoft Teams SDK update.
This attack is similar to a ClickFix attack, in which victims are shown a fake error message and then prompted to follow troubleshooting steps that deploy malware.
This attack also mirrors previous campaigns reported by Google’s threat intelligence teams, in which North Korean threat actors tracked UNC1069 used the same tactics to target cryptocurrency firms.
In previous campaigns attributed to the UNC1069 threat actor, the threat actors would deploy additional payloads on devices, such as backdoors, downloaders, and infostealers designed to steal credentials, browser data, session tokens, and other sensitive information.
Since the attackers gained access to authenticated sessions, MFA protections were effectively bypassed, allowing access to accounts without having to re-authenticate.
The Axios maintainers confirmed that the attack did not involve modifying the project’s source code, but instead relied on injecting a malicious dependency into otherwise legitimate releases.
Pelle Wessman, a maintainer of numerous open-source projects, including the popular Mocha framework, posted on LinkedIn that he was targeted in the same campaign and shared a screenshot of a fake RTC connection error message used to trick targets into installing malware.
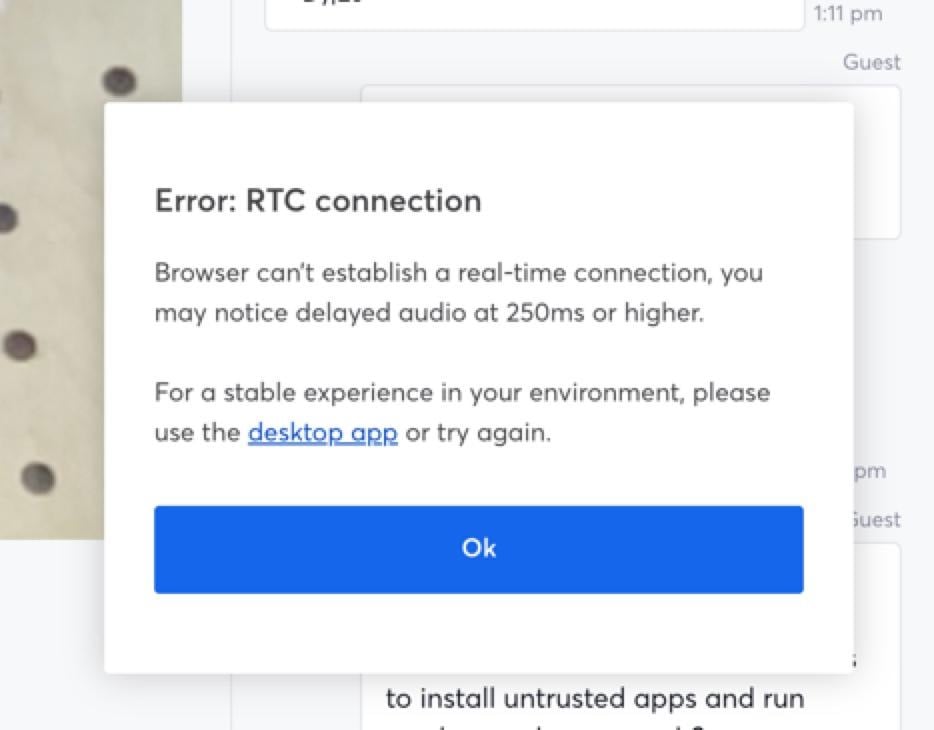
Source: Pelle Wessman
When Wessman refused to install the app, the threat actors tried to convince him to run a Curl command.
“When it became clear that I wouldn’t run the app and we had chatted back and forth on website and chat app they made one final desperate attempt and tried to get me to run a curl command that would download and run something, then when I refused they went dark and deleted all conversations,” explained Wessman.
Cybersecurity firm Socket also reported that this was a coordinated campaign that has begun targeting maintainers of popular Node.js projects.
Multiple developers, including maintainers of widely used packages and Node.js core contributors, reported receiving similar outreach messages and invitations to Slack workspaces operated by the attackers.
Socket noted that these maintainers are responsible for packages with billions of weekly downloads, demonstrating that the threat actors focused on high-impact projects.
“Since we published our initial analysis of the axios compromise, a deep dive into its hidden blast radius, and a report on the maintainer confirming it was social engineering, maintainers across the Node.js ecosystem have come out of the woodwork to report that they were targeted by the same social engineering campaign,” explained Socket.
“The accounts now span some of the most widely depended-upon packages in the npm registry and Node.js core itself, and together they confirm that axios was not a one-off target. It was part of a coordinated, scalable attack pattern aimed at high-trust, high-impact open source maintainers.”
Socket said the campaign followed a consistent pattern, with the threat actors first making contact through platforms like LinkedIn or Slack and then inviting recipients into private or semi-private workspaces.
After building rapport with the target, the threat actors scheduled video calls, which in some cases were conducted through sites impersonating Microsoft Teams and other platforms.
During these calls, an error message would be displayed to the targets, which prompted them to install “native” desktop software that works better or run commands to fix the technical issues.
The same playbook used against all these targets during the same time period indicates this was a coordinated campaign rather than a series of one-off attacks.
The Socket researchers say that these types of supply chain attacks are becoming more common, with attackers now focusing on widely used packages to cause widespread impact.
Automated Pentesting Covers Only 1 of 6 Surfaces.
Automated pentesting proves the path exists. BAS proves whether your controls stop it. Most teams run one without the other.
This whitepaper maps six validation surfaces, shows where coverage ends, and provides practitioners with three diagnostic questions for any tool evaluation.
Related Articles:
Hackers compromise Axios npm package to drop cross-platform malware
North Korean hackers use new macOS malware in crypto-theft attacks
Not a Kids Game: From Roblox Mod to Compromising Your Company
Popular LiteLLM PyPI package backdoored to steal credentials, auth tokens
Trivy vulnerability scanner breach pushed infostealer via GitHub Actions
