We often treat cloud-based password managers as digital safes that only we can open. These services rely on Zero-Knowledge Encryption, a marketing promise that the company storing your data cannot actually see what is inside. However, new research suggests that this safety net is not as secure as many of us assume.
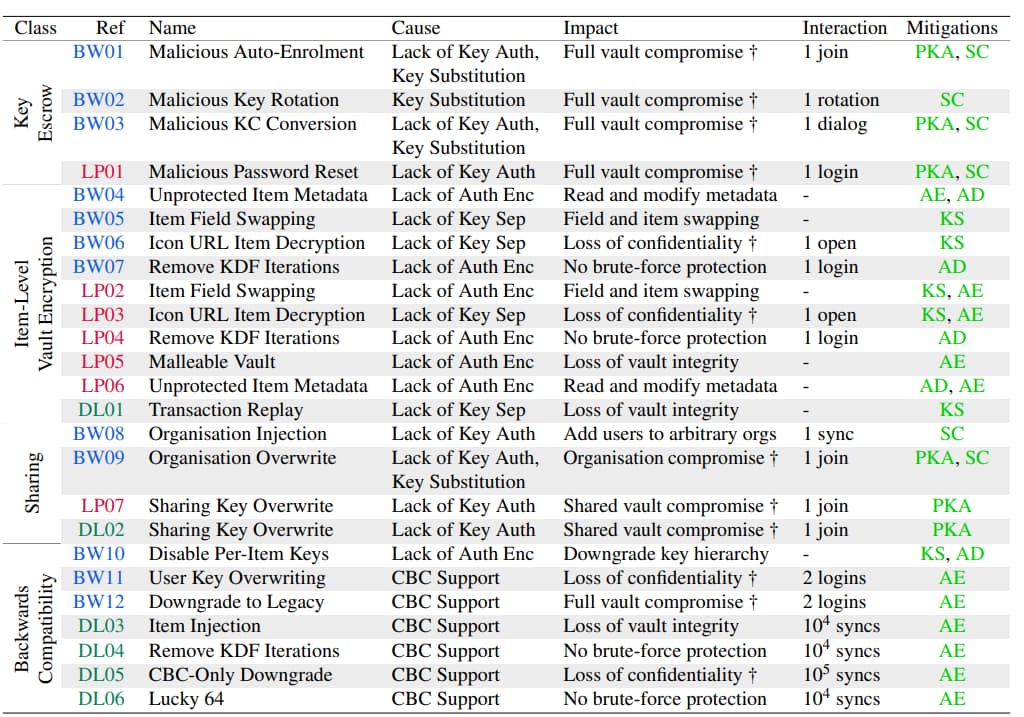
A group of researchers from ETH Zurich and the Università della Svizzera italiana, led by Professor Kenneth Paterson, recently released a paper that should make every security-conscious person concerned. The team executed 27 successful attacks against industry leaders Bitwarden, LastPass, and Dashlane (12 against Bitwarden, 7 against LastPass, and 6 against Dashlane), proving that if a server is compromised by a sophisticated actor, your vault can be unlocked with surprising ease.
How the Vaults Were Broken
The findings dismantle the main promise of Zero-Knowledge. Using a Malicious Server Model, researchers showed that a hacked server could trick the app into betraying the user. These apps often fail to verify if data from the central server has been tampered with, a flaw known as a lack of ciphertext integrity and cryptographic binding, where the metadata (like the URL) isn’t properly locked to the sensitive data (the password).
In a field swap attack against Bitwarden and LastPass, researchers showed that because logins are saved in separate pieces (username, password, and URL), a hacker on the server can swap them. By moving your encrypted password into the URL spot, the app may accidentally send your decrypted password to an attacker’s server while simply trying to load a website icon.
Other attacks targeted features like account recovery and sharing. In a Malicious Auto-Enrolment attack, a compromised server can force a user to join a fake organisation. Because the app does not authenticate public keys, it might “blindly trust” the server and encrypt the user’s master key using the attacker’s key. This hands over a “recovery ciphertext” that the hacker can easily unlock.
Furthermore, researchers exploited a Legacy Hazard, where apps keep 15-year-old security methods active for backward compatibility, allowing attackers to force a KDF downgrade to guess data byte-by-byte.
Which Apps are Safest and What to Do
While Bitwarden, LastPass, and Dashlane showed various weaknesses, 1Password emerged as the most secure. Researchers found that 1Password’s Secret Key, a random code that stays only on your devices, makes most of these server-side attacks mathematically impossible. Even if a hacker takes over the company’s servers, they lack the second half of the key needed to decrypt the data. This highlights that true digital safety requires a small extra step from the user rather than total reliance on a company’s marketing.
Following the study’s 90-day disclosure period, vendors have begun patching these holes. Dashlane and Bitwarden have already released fixes to harden their systems and remove legacy cryptography. Users should update their apps immediately.
To maximise protection, enable a Secret Key or use a hardware security key (like a YubiKey); these add a physical layer of security that a remote hacker simply cannot bypass. Apart from that, researchers conclude that vendors also need to “ensure solid foundations, novel definitions to capture security in this setting.”