
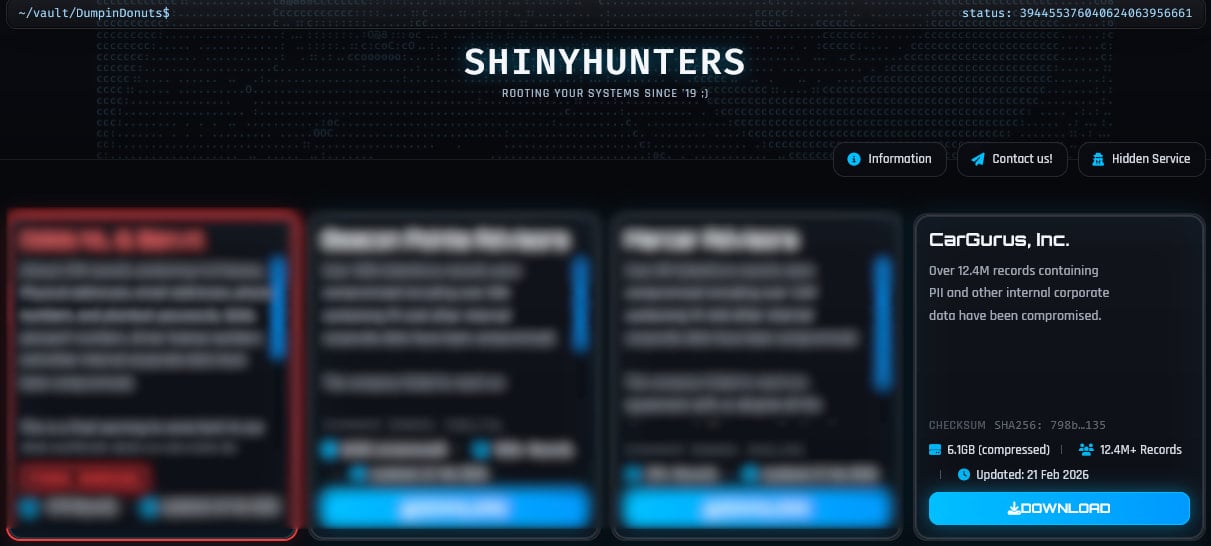
The ShinyHunters extortion group has published personal information in more than 12 million records allegedly stolen from CarGurus, a U.S.-based digital auto platform.
CarGurus is a publicly traded automotive research and shopping company that operates in the U.S., Canada, and the U.K. Its website has an estimated 40 million monthly visitors and helps people find, compare, and contact sellers of new and used vehicles.
On February 21, the threat group published a 6.1GB archive containing 12.4 million records, saying it was from CarGurus. A day later, the HaveIBeenPwned (HIBP) data breach monitoring and alerting platform added the dataset, listing the following data types as compromised:
- Email addresses
- IP addresses
- Full names
- Phone numbers
- Physical addresses
- User account IDs
- Finance pre-qualification application data
- Finance application outcomes
- Dealer account details
- Subscription information
Although CarGurus has not released an official statement disclosing a data breach and did not respond to BleepingComputer’s request for comment, it is important to note that HIBP attempts to confirm the validity/authenticity of the leaked records before adding them.
HIBP reports that 70% of the leaked data was already on its database from previous incidents, so roughly 3.7 million records are fresh. Since the information is freely available for download, cybercriminals could take advantage of it for phishing attacks.
Source: BleepingComputer
CarGurus users are advised to stay alert for potentially malicious communications and scam attempts leveraging the leaked information.
The ShinyHunters data extortion group has been very active recently, claiming multiple attacks on large companies and leaking their data when negotiations reached a dead end.
The most recent examples include Dutch telecommunications provider Odido, ad tech firm Optimizely, fintech firm Figure, outerwear brand Canada Goose, restaurant chain Panera Bread, online dating company Match Group, and music streaming platform SoundCloud.
The threat group typically uses social engineering, most commonly voice phishing, to breach organizations, directing victims to credential-harvesting pages that grant them access to SaaS platforms such as Salesforce, Okta, and Microsoft 365.
Previous ShinyHunters campaigns also involved tricking employees into installing malicious OAuth applications that granted them API-level read access to customer data tables inside Salesforce instances.
The future of IT infrastructure is here
Modern IT infrastructure moves faster than manual workflows can handle.
In this new Tines guide, learn how your team can reduce hidden manual delays, improve reliability through automated response, and build and scale intelligent workflows on top of tools you already use.
Related Articles:
Have I Been Pwned: SoundCloud data breach impacts 29.8 million accounts
Data breach at fintech firm Figure affects nearly 1 million accounts
Canada Goose investigating as hackers leak 600K customer records
Panera Bread breach impacts 5.1 million accounts, not 14 million customers
Match Group breach exposes data from Hinge, Tinder, OkCupid, and Match

