A coordinated international operation has dismantled one of the most widely used phishing platforms designed to bypass multi-factor authentication. The service, known as Tycoon 2FA, powered large-scale credential theft campaigns that targeted organisations worldwide.
The operation, led by Europol, brought together investigators, cybersecurity companies, and infrastructure providers to dismantle the service’s infrastructure. As part of the disruption, authorities and industry partners seized hundreds of domains and disabled key components of the platform’s phishing infrastructure.
A phishing service built for scale
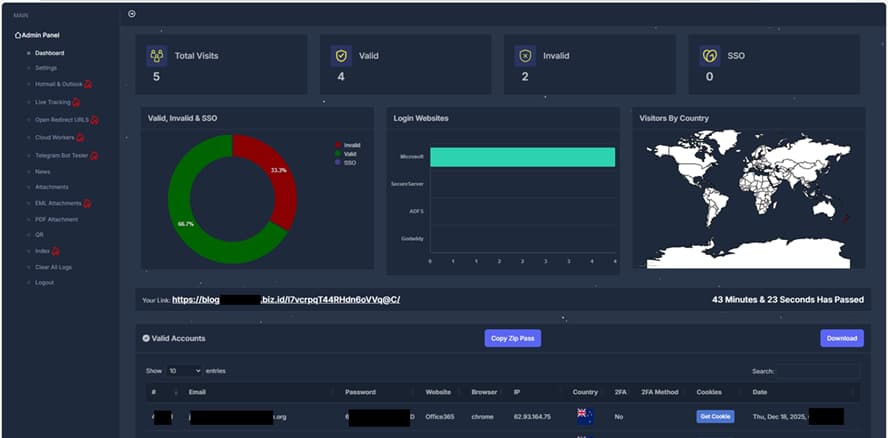
Tycoon 2FA operated as a phishing-as-a-service (PhaaS) offering cybercriminals a ready-made toolkit to run credential-harvesting campaigns with little technical expertise. Subscribers could rent access through encrypted messaging channels such as Telegram, paying around $120 for short-term access or more for full panel control.
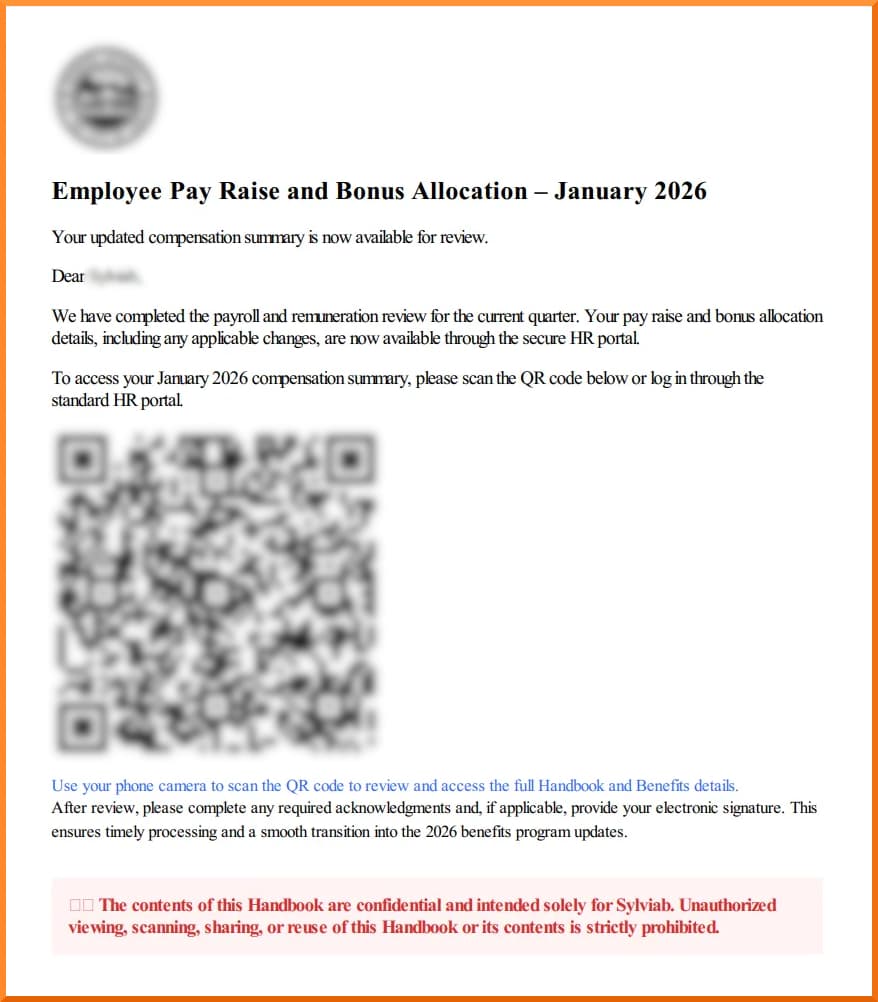
The paid package included phishing templates that mimicked widely used platforms such as Microsoft 365, Outlook, and Gmail, along with hosting infrastructure and dashboards that tracked victims in real time.
Because the service was packaged as a subscription, even inexperienced attackers could deploy convincing phishing campaigns at scale. By mid-2025, security telemetry linked the platform to tens of millions of phishing emails every month and attacks targeting more than 500,000 organisations globally.
How the kit bypassed multi-factor authentication
Traditional phishing kits usually stop at stealing usernames and passwords. Tycoon 2FA went further by using a technique known as adversary-in-the-middle phishing. In practice, the kit placed a proxy server between a victim and the legitimate login service.
When a target entered their credentials and authentication code on a convincing look-alike login page, the proxy forwarded the information to the real service while quietly capturing the session token generated after login.
That session token allowed attackers to hijack the authenticated session without needing the password or authentication code again. In many cases, criminals could maintain access even if the victim later changed their password, because the stolen session remained valid until revoked.
This capability made the platform attractive for account takeover campaigns that often escalated into business email compromise, financial fraud, and network intrusions.
Origins and early development
Tycoon 2FA first surfaced in August 2023 and quickly gained a reputation within cybercrime forums and messaging channels. Researchers believe the framework evolved from earlier phishing kits, including a fork of the DadSec/Phoenix phishing kit, which had already demonstrated how reverse-proxy phishing could bypass authentication protections.
The service rapidly matured into a commercialised platform. Operators maintained an organized network that included developers, customer support, marketing, and payment channels. Investigators believe development activity may have originated in Pakistan, while many subscribers were distributed across West Africa and other regions.
Nevertheless, the result was a global phishing platform capable of targeting enterprises, government agencies, healthcare organisations, and universities. Security data collected from exposed control panels shows that hundreds of thousands of victim credentials were harvested during the platform’s active period.
Inside the global investigation
According to Europol’s press release, the takedown followed months of intelligence gathering and cooperation between law enforcement and private cybersecurity companies. Early threat intelligence shared by researchers helped investigators map the platform’s infrastructure and identify the domains used to host phishing pages and control panels.
Authorities in several European countries, including the United Kingdom, Spain, Poland, Portugal, Latvia, and Lithuania, participated in the coordinated action. Meanwhile, technology companies contributed infrastructure analysis, victim telemetry, and threat intelligence to support the investigation.
As part of the disruption effort, investigators seized around 330 domains used by the platform and disabled hosting resources linked to the phishing infrastructure. The investigation also involved infiltrating the criminal service itself. Security researchers reportedly posed as customers to gain insight into the platform’s tools, payment channels, and operational structure, helping build the evidence needed to disrupt the network.
While the disruption removes a cybercrime platform, researchers warn that similar services are likely to appear. Reverse-proxy phishing frameworks remain one of the most effective ways to bypass traditional authentication protections, particularly when organisations rely solely on standard multi-factor authentication.