A massive security gap has been brought to light by the research firm GitGuardian in partnership with Google. The study reveals that the private keys used to protect some of the world’s most important websites are being left wide open for anyone to find
These keys, as we know them, are the backbone of TLS certificates, the technology that puts the padlock in your browser and keeps your credit card details or passwords safe. These certificates use a pair of keys: a public one that everyone can see, and a private one that must stay secret, so if a private key leaks, the encryption is basically broken.
Fortune 500 and Governments at Risk
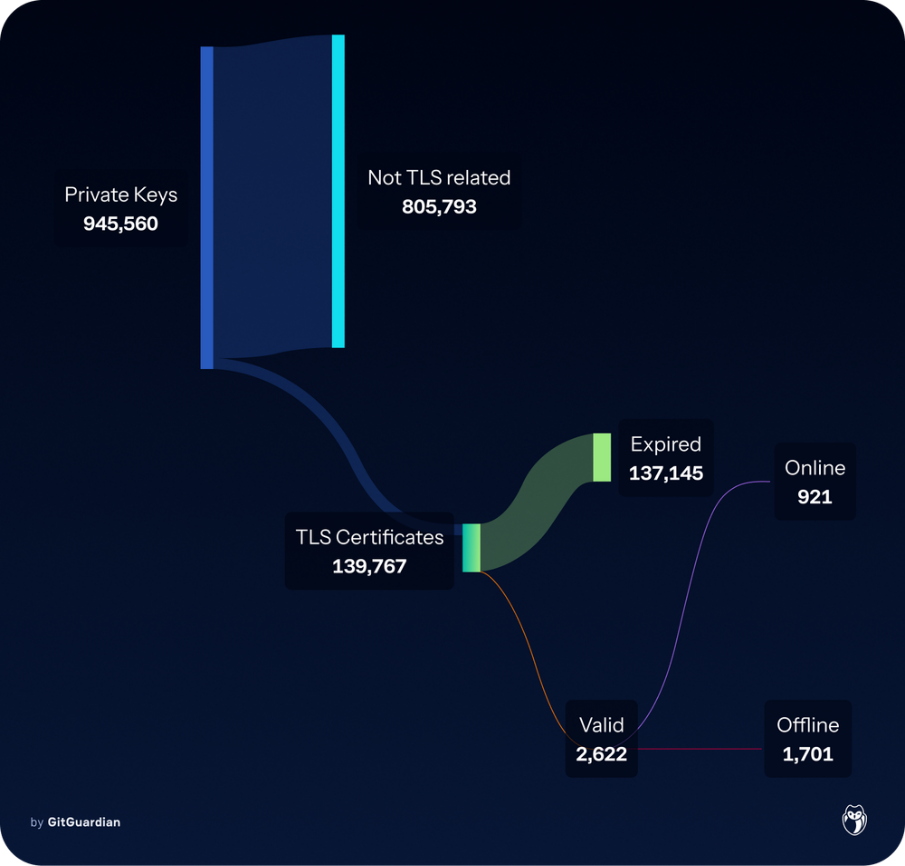
GitGuardian researchers noted in the blog post, shared with Hackread.com, that since 2021, they have tracked roughly one million unique private keys accidentally posted to public code sites like GitHub and DockerHub. By cross-referencing these with Google’s massive database of web records, they mapped these leaks to 140,000 real-world certificates.
Further investigation revealed a worrying reality: as of September 2025, exactly 2,622 of these certificates were still valid and active. For your information, more than 900 of these were protecting Fortune 500 companies, healthcare providers, and even government agencies.
When these keys leak, the danger is immediate. “A compromised key enables attackers to impersonate websites or intercept data,” the researchers explained. Despite this, it seems many big organisations are completely unaware of the threat sitting right under their noses.
The Struggle to Find Ghost Owners
It is worth noting that even when the researchers found a leak, they had no idea who it belonged to. Out of the 2,600 valid certificates, a mere 16% actually contained any information about the organisation that owned them.
To solve this, the team had to scrape website records, check domain ownership, and even use AI-assisted web crawling just to find an email address. Despite these efforts, roughly 1,300 certificates remained untraceable, leaving those websites permanently at risk because the owners couldn’t be found.
A Lack of Urgency
Even when owners were identified, the response was poor. The team sent out 4,300 disclosure emails to over 600 organisations, but only 9% bothered to reply. According to researchers, some bug bounty programmes even asked for proof that having a website’s private key was actually a security problem.
Eventually, the team reached a 97% remediation rate, but only after going directly to the authorities that issue the certificates. The researchers concluded that the industry must move toward single-use keys that rotate automatically, ensuring that even if a leak happens, the damage is limited.
Deeba Ahmed