Cisco has issued security updates addressing dozens of vulnerabilities affecting several of its firewall platforms, including Cisco Secure Firewall Adaptive Security Appliance, Cisco Secure Firewall Management Center, and Cisco Secure Firewall Threat Defense. The release contains 25 advisories covering 48 flaws across the widely deployed network security products.
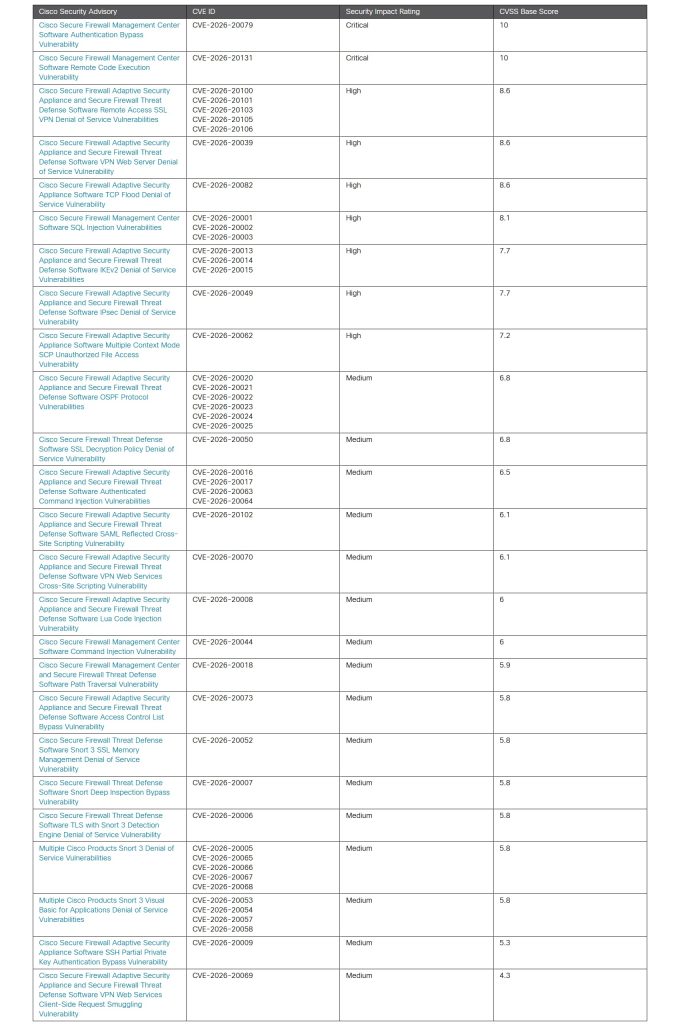
The updates were published together as part of a bundled advisory set, a format Cisco occasionally uses when multiple related issues are addressed at once. Among the vulnerabilities, two stand out for their severity. Both carry a maximum Common Vulnerability Scoring System (CVSS) score of 10 and affect Cisco Secure Firewall Management Center software, the centralized management platform used to control and monitor firewall deployments.
One of the most serious issues, CVE-2026-20079, is an authentication bypass flaw. The problem stems from an improperly created system process during device startup. An attacker could exploit the weakness by sending specially crafted HTTP requests to a vulnerable device. If successful, the attacker could run scripts or commands that grant root-level access to the system.
The second critical vulnerability, CVE-2026-20131, involves insecure deserialization within the product’s web-based management interface. In practical terms, an attacker could send a malicious serialized Java object to the interface and trigger remote code execution. Once exploited, the flaw allows arbitrary code to run on the device, with the possibility of escalating privileges to root.
Other than these two critical vulnerabilities, Cisco’s advisory package also includes 15 high-severity vulnerabilities with scores ranging from 7.2 to 8.6, along with 31 medium-severity flaws rated between 4.3 and 6.8. Collectively, they affect core firewall services and management components that are commonly deployed across enterprise networks.
It is worth noting that Cisco says there are no temporary fixes for the two critical vulnerabilities. The only way to address them is to upgrade to the patched software versions listed in the advisory, which Cisco recommends organizations do as soon as possible.
Expert Views
Cybersecurity experts say large coordinated patch releases like this are not unusual in enterprise infrastructure products, even when the vulnerability count appears high. David Brumley, Chief AI and Science Officer at Bugcrowd, a San Francisco, Calif.-based leader in crowdsourced cybersecurity, said the size of the release reflects how vendors often handle clusters of related flaws.
“This update has an unusually large number of vulnerabilities remediated, but that isn’t necessarily a red flag. It’s quite common for enterprise products to release coordinated fixes on a regular schedule. Batching patches also helps vendors and organizations test patches for unintended side effects or downtime.”
Brumley noted that the bundled release appears to follow a series of related discoveries earlier in the year. “This update in particular seems to be because a large number of new, related vulnerabilities reported earlier in the year. When you have related vulnerabilities, it’s often better to patch them all together. The important signal here is that the vulnerabilities being patched are critical and actively exploited. I recommend everyone apply these patches as quickly as possible.”
The urgency partly stems from the role firewalls play in modern networks. Positioned at the boundary between internal systems and the public internet, they are among the most exposed devices in an organization’s infrastructure.
“Firewalls sit directly on the network perimeter, which means they are exposed to the internet and reachable by attackers. If an attacker finds a vulnerability in a firewall or its management system, they can often bypass or disable the very defenses meant to stop them,” Brumley explained.
That exposure has made network edge infrastructure a persistent target for sophisticated threat actors. “Targeting of network edge devices, especially firewalls, VPN gateways, and routers, has been a consistent trend in advanced cyber operations. Nation-state actors in particular often target these systems in telecom providers, government networks, and critical infrastructure because they provide both access and surveillance opportunities.”
Brumley also pointed to a growing challenge facing defenders: the speed at which newly disclosed vulnerabilities are turned into working exploits.
“One new trend we’re seeing is faster weaponization of 1-day vulnerabilities. I think AI is playing a part here. One problem is finding new zero-days, where the AI doesn’t have much information. In 1-days, you can point at the exact place in the code vulnerable, and that makes it much easier for the AI to reason and exploit.”
With no temporary mitigations available for the most severe flaws, companies running Cisco Secure Firewall environments are advised to review Cisco’s advisory and prioritize patch deployment to reduce exposure.