In 2020, Brazil changed the way its citizens handle money by launching PIX, an instant payment system that now processes billions of transactions every month. But that speed has come with a price. A new Android threat, named PixRevolution, has been caught hijacking these payments exactly as they happen.
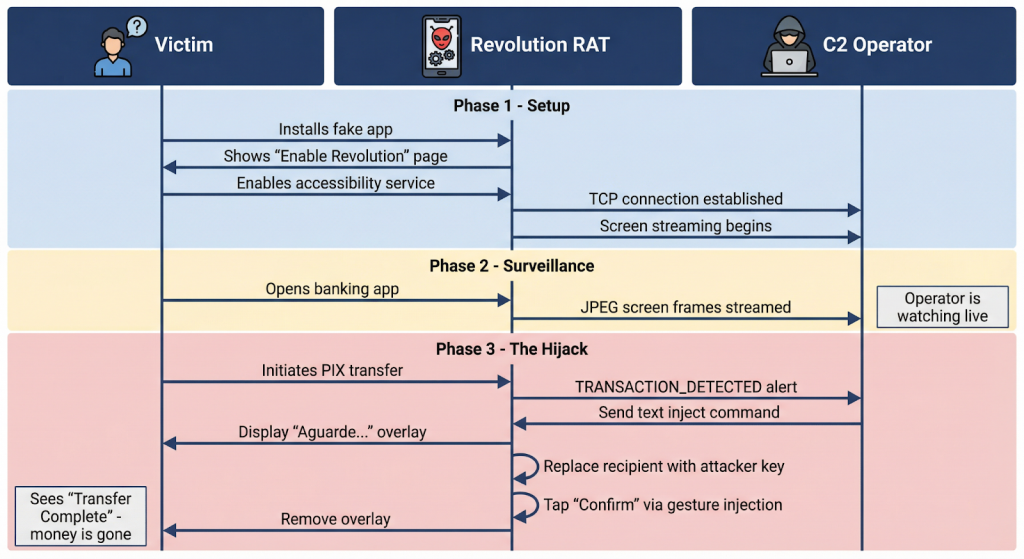
According to security experts at the firm Zimperium, who shared their latest research exclusively with Hackread.com, this isn’t like a typical automated virus because it relies on an agent-in-the-loop model. This means that on the other end of the connection, a human or an AI operator is literally watching a live stream of your phone screen, waiting for the perfect second to strike.
A Fake Wait Screen While Money Vanishes
The scam is surprisingly simple but effective. When a victim starts a PIX transfer, the malware throws up a full-screen loading spinner that says “Aguarde…” (please wait). While the user is staring at that spinner, the hacker is busy behind the scenes.
Further probing revealed that the malware identifies the text field where the user typed the recipient’s key and swaps it with the attacker’s own info. It then simulates a tap on the confirm button. By the time the loading screen disappears, the transaction is finished. As we know it, PIX transfers are instant and irrevocable, so once that money hits the criminal’s account, it is effectively gone for good.
How the Infection Starts
As per Zimperium’s blog post, these hackers aren’t using the official Google Play Store. They build fake websites that look identical to the real store to trick people into downloading dropper apps. These apps often masquerade as popular services like Expedia, the Postal Service (Correios), or even government tools like the Superior Court (STJ).
Once installed, the app tricks the user into enabling Accessibility Services. Researchers noted that the app even gives step-by-step instructions for Samsung, Xiaomi, and Motorola users to make sure they turn it on. Please note that this permission allows the malware to read everything on the screen and interact with other apps.
Hard to Detect
It is worth noting that this malware doesn’t care which bank you use because it monitors your screen for over 80 specific Portuguese phrases related to money, such as pix enviado (pix sent) or saldo insuficiente (insufficient balance). It even carries logos for 10 major banks, including Nubank, Itaú, and Santander, just to make its fake overlays look more convincing.
The scariest part? From the victim’s perspective, nothing seemed wrong. The phone just lagged for a second during a normal payment. Experts suggest that because these hackers are watching in real-time, traditional security that looks for old patterns might not always catch them.