
A new open-source tool called Betterleaks can scan directories, files, and git repositories and identify valid secrets using default or customized rules.
Secret scanners are specialized utilities that scour repositories for sensitive information, such as credentials, API keys, private keys, and tokens, that developers accidentally committed in source code.
Since threat actors often scan configuration files in public repositories for sensitive details, this type of utility can help identify secrets and protect them before attackers can find them.
The new Betterleaks project is intended as a more advanced successor to Gitleaks and is maintained by the same team, with support from Aikido, a Belgian company that provides a platform for securing the development cycle.
Source: GitHub
Betterleaks is developed by Zach Rice, Head of Secrets Scanning at Aikido Security, who also authored the popular Gitleaks with 26 million downloads on GitHub and more than 35 million pulls on Docker and GitHub Container Registry (GHCR).
“Betterleaks is the successor to Gitleaks. We’re dropping the “git” and slapping “better” on it because that’s what it is, better,” Rice says.
Betterleaks was created after Rice lost full control over Gitleaks, which he started developing eight years ago. The list of features in the new tool includes:
- Rule-defined validation using CEL (Common Expression Language)
- Token Efficiency Scanning based on BPE tokenization rather than entropy, achieving 98.6% recall vs 70.4% with entropy on the CredData dataset
- Pure Go implementation (no CGO or Hyperscan dependency)
- Automatic handling of doubly/triply encoded secrets
- Expanded rule set for more providers
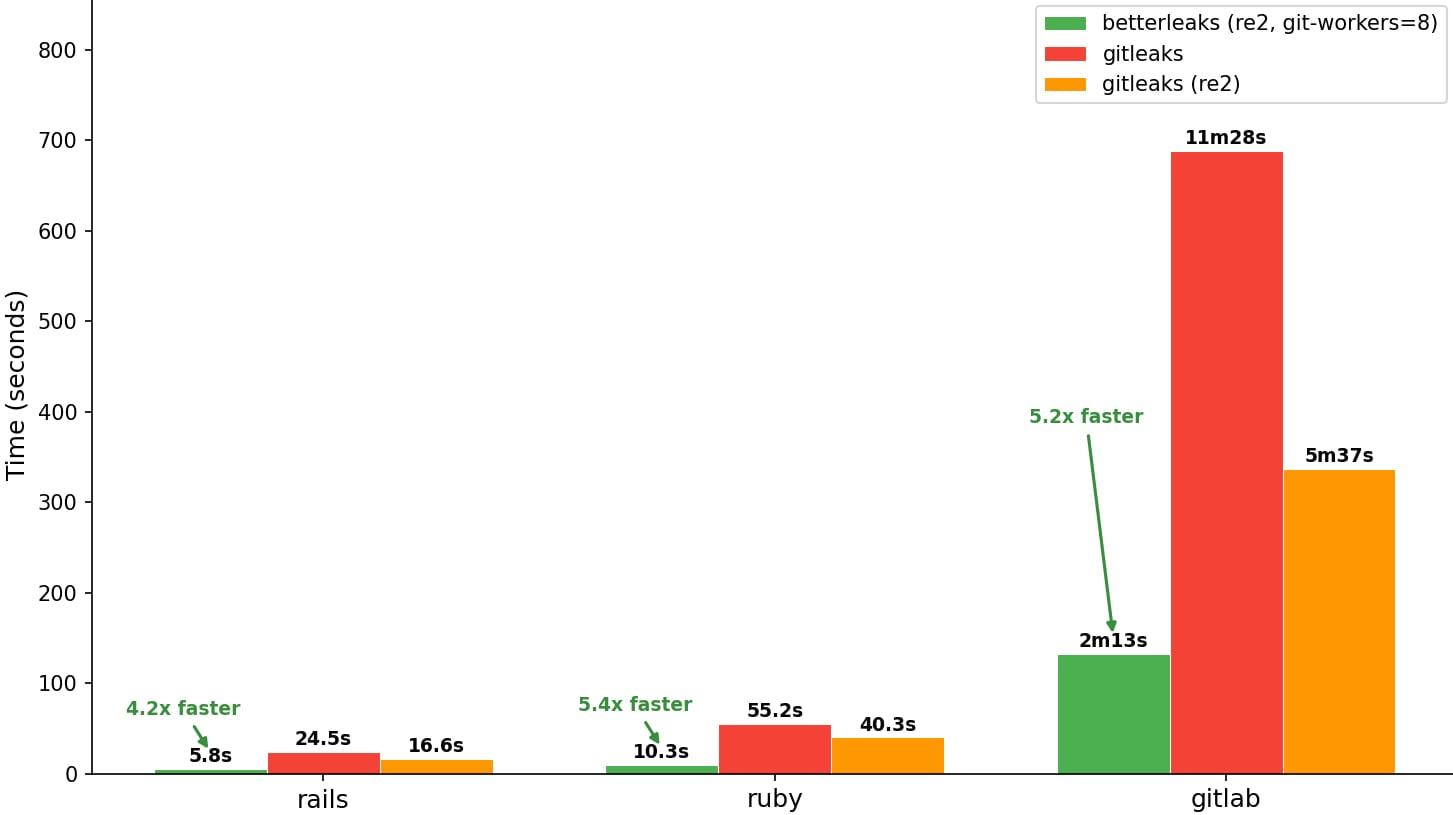
- Parallelized Git scanning for faster repository analysis
The developer has also revealed additional features planned for the next version of Betterleaks, like support for additional data sources beyond Git repositories and files, LLM-assisted analysis for better secret classification, more detection filters, automatic secret revocation via provider APIs, permissions mapping, and performance optimizations.
Regarding the project’s governance, Rice explains that it uses the open-source MIT license and is maintained by three additional people beyond himself, including contributors from the Royal Bank of Canada, Red Hat, and Amazon.
Rice underlined that Betterleak’s design philosophy combines human-centric use with accommodation for AI agent workflows, including CLI features optimized for automated tools that scan AI-generated code.
Red Report 2026: Why Ransomware Encryption Dropped 38%
Malware is getting smarter. The Red Report 2026 reveals how new threats use math to detect sandboxes and hide in plain sight.
Download our analysis of 1.1 million malicious samples to uncover the top 10 techniques and see if your security stack is blinded.
Related Articles:
Hackers can bypass npm’s Shai-Hulud defenses via Git dependencies
Bing AI promoted fake OpenClaw GitHub repo pushing info-stealing malware
CyberStrikeAI tool adopted by hackers for AI-powered attacks
Previously harmless Google API keys now expose Gemini AI data
Bitwarden introduces ‘Cupid Vault’ for secure password sharing
