In a world where many of us move constantly from one video call to the next, a clever new trick is being used to break into home and office computers. Researchers from Sublime Security recently reported a scam that uses a very realistic, but entirely fake, Zoom meeting to trick people into downloading malware.
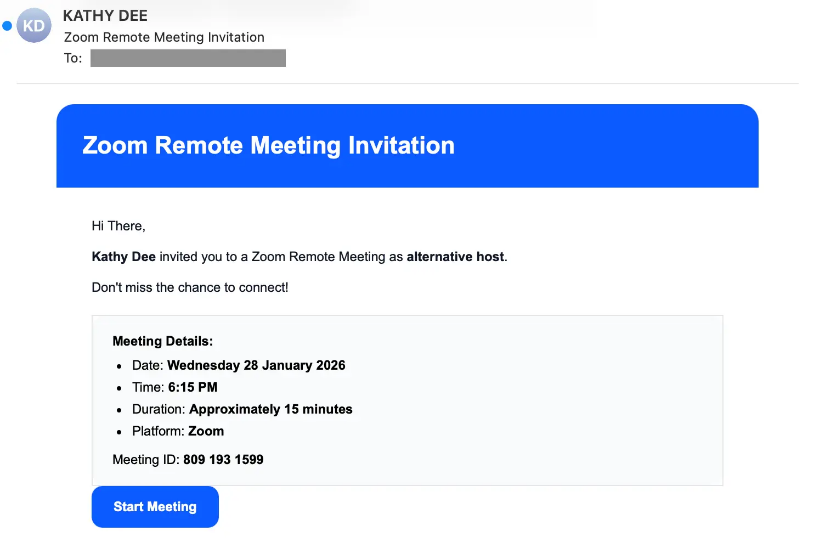
The attack usually begins with a simple email that looks exactly like a standard Zoom invitation, featuring a large button to start the meeting. However, instead of going to the official Zoom website, it launches a series of fake security checks.
A scripted waiting room
Researchers explained that after the user passes a spoofed security test, a screen appears that looks exactly like a Zoom waiting room, even showing how long the meeting is supposed to last and how many people are already there. If the person is using a Windows computer, the scam continues; it stops when it detects a system such as an Apple Mac.
According to Sublime Security’s blog post, shared with Hackread.com, the most surprising part is what happens after you click join. Instead of a real call, the browser runs JavaScript to create a live, interactive simulation of a meeting. This allows scammers to include fictitious participants such as Matthew Karlsson and Sarah Chen. To make it feel real, the script even triggers choppy audio and warnings about a Network Issue, but this is just a trick to make the user believe their software is glitching and needs a fix.
The trap is set
Software updates, as we know them, are a regular part of digital life; therefore, when a pop-up appears during this fake call saying “Update Available,” many do not think twice. The site then redirects to a fake Microsoft Store page to download the file. However, this file actually installs a tool called ScreenConnect. While this is a real tool used by IT departments to help people remotely, in this case, it is set up to give the attackers complete control over the victim’s computer.
Researchers highlighted several clues that indicate the invite was a fake. For instance, the emails came from a standard Gmail address rather than an official company account, and the website address for the meeting was entirely unrelated to Zoom.
A growing trend of platform abuse
“Zoom abuse and impersonation have become popular lure tactics for attackers,” Sublime researchers noted, adding that this latest attempt stood out because of the extreme lengths the hackers went to fool people.
Previous coverage from Hackread.com has also noticed a pattern of hackers exploiting the Zoom platform. We’ve reported similar campaigns in March 2026, where hackers used convincing clones of waiting rooms and fake certificates to deploy stealthy employee monitoring tools that log keystrokes and record screens.