
The U.S. Federal Bureau of Investigation (FBI) warned network defenders that Iranian hackers linked to the country’s Ministry of Intelligence and Security (MOIS) are using Telegram in malware attacks.
In a flash alert issued on Friday, the FBI says Telegram is being used as command-and-control (C2) infrastructure by malware targeting journalists criticizing the Iranian government, Iranian dissidents, and various other oppositional groups worldwide.
The bureau linked these attacks to the Iranian-linked and pro-Palestinian Handala hacktivist group (also known as Handala Hack Team, Hatef, Hamsa) and the Iranian state-sponsored Homeland Justice threat group tied to Iran’s Islamic Revolutionary Guard Corps (IRGC).
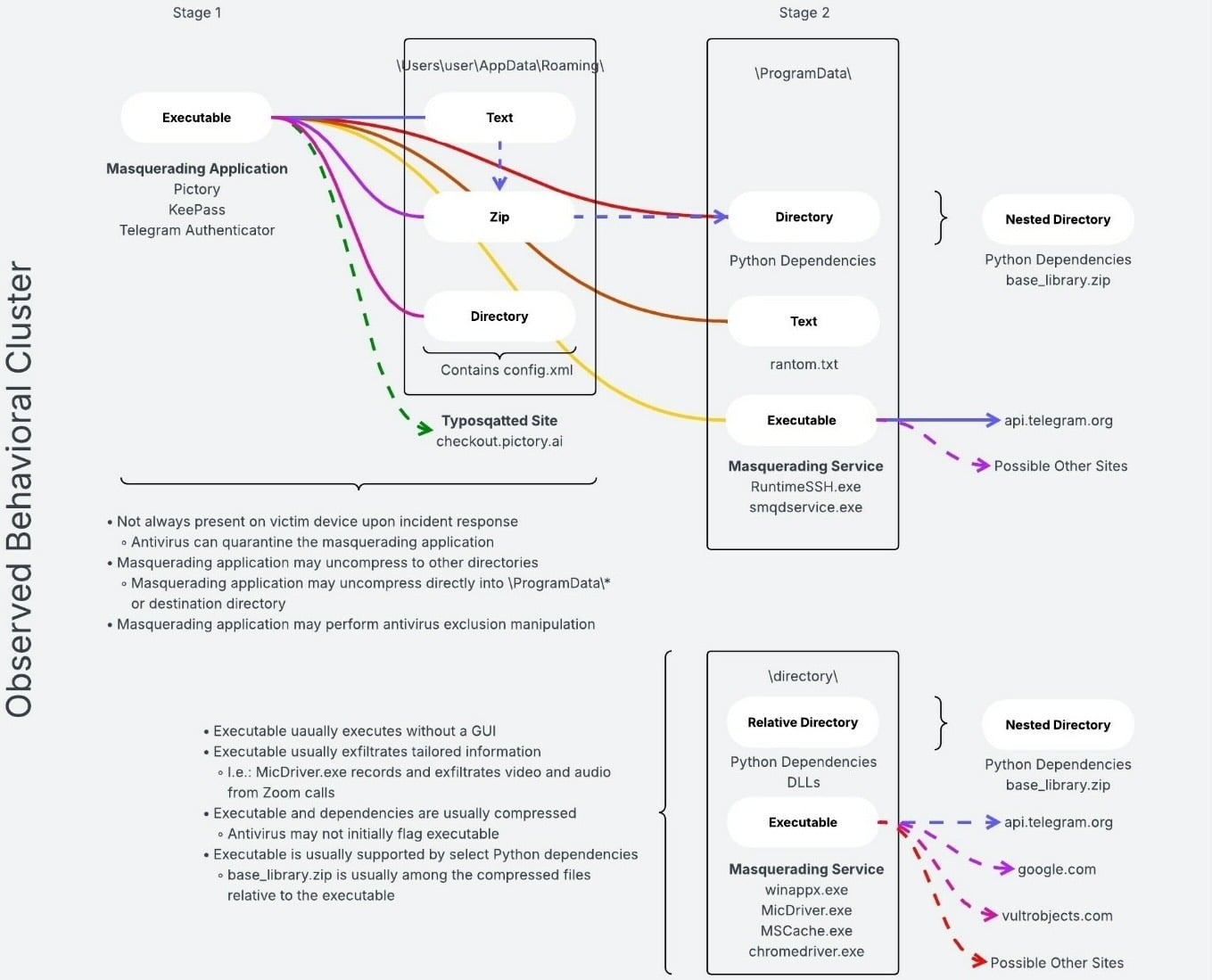
In these attacks, the Iranian hackers are using social engineering to infect targets’ devices with Windows malware that enables them to exfiltrate screenshots or files from compromised computers.
“Due to the elevated geopolitical climate of the Middle East and current conflict, the FBI is highlighting this MOIS cyber activity,” the bureau said.
“This malware resulted in intelligence collection, data leaks, and reputational harm against the targeted parties. The FBI is releasing this information to maximize awareness of malicious Iranian cyber activity and provide mitigation strategies to reduce the risk of compromise.”
This warning was published one day after the FBI seized four domains (handala-redwanted[.]to, handala-hack[.]to, justicehomeland[.]org, and karmabelow80[.]org).
The websites available via the seized clearnet domains were used by the Handala and Homeland Justice threat groups, and a third threat actor tracked as Karma Below, during their attacks and to leak sensitive documents and data stolen in cyberattacks targeting victims in the United States and around the world.
These actions follow Handala’s cyberattack on U.S. medical giant Stryker, in which they factory reset approximately 80,000 devices (including employees’ personal computers and mobile devices managed by the company) using the Microsoft Intune wipe command after compromising a Windows domain administrator account and creating a new Global Administrator account.
Last week, the FBI also warned that Russian intelligence-linked threat actors are targeting Signal and WhatsApp users in phishing campaigns that have already compromised thousands of accounts.
“The activity targets individuals of high intelligence value, such as current and former U.S. government officials, military personnel, political figures, and journalists,” said the FBI in a public service announcement issued after Dutch and French cybersecurity authorities described similar account-hijacking operations.
Red Report 2026: Why Ransomware Encryption Dropped 38%
Malware is getting smarter. The Red Report 2026 reveals how new threats use math to detect sandboxes and hide in plain sight.
Download our analysis of 1.1 million malicious samples to uncover the top 10 techniques and see if your security stack is blinded.
Related Articles:
FBI seizes Handala data leak site after Stryker cyberattack
FBI seeks victims of Steam games used to spread malware
Medtech giant Stryker offline after Iran-linked wiper malware attack
Google adds ‘Advanced Flow’ for safe APK sideloading on Android
FBI links Signal phishing attacks to Russian intelligence services
