
Fraud operations have expanded beyond traditional hacking techniques to include methods that exploit legitimate services and real-world infrastructure. By combining publicly available data, weak identity verification processes, and operational gaps, threat actors are building scalable fraud workflows that are both low-cost and difficult to detect.
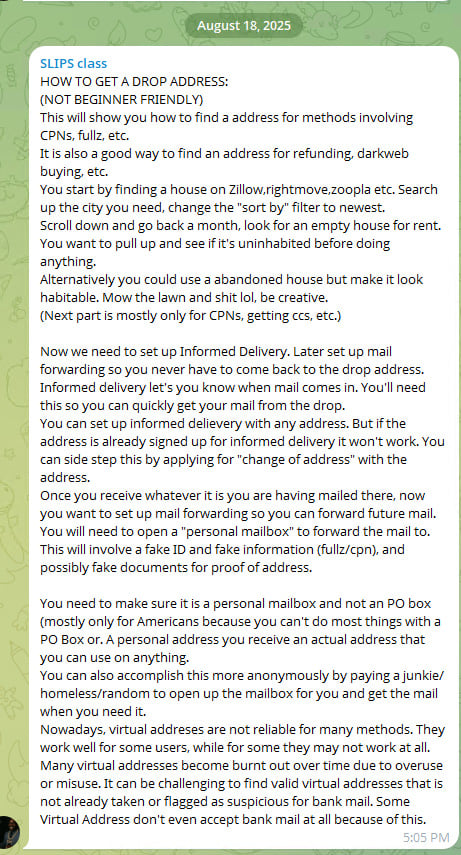
A tutorial shared in a fraud-focused chat group and analyzed by Flare analysts provides step-by-step guidance on how to identify and exploit vacant residential properties to intercept sensitive mail, revealing a low-tech but highly effective method for enabling identity theft and financial fraud.
Unlike traditional cybercrime techniques that rely on malware, phishing kits, or network intrusions, the method outlined in this article focuses almost entirely on abusing legitimate services and physical-world logistics.
The approach blends open-source intelligence, postal service features, and fake identity fraud into a coordinated workflow designed to gain persistent access to victims’ mail.
Turning vacant properties into fraud infrastructure
The tutorial begins with identifying so-called “drop addresses”, real residential properties that are temporarily unoccupied and can be used to receive mail without immediately alerting the rightful occupants.
Threat actors are instructed to search real estate platforms such as Zillow, Rightmove, or Zoopla, filtering for recently listed rental properties. By focusing on newly available listings, attackers increase the likelihood that the property is vacant or between tenants.
The guidance further suggests reviewing older listings to identify homes that have remained unoccupied for extended periods, increasing their reliability as drop locations.
In some cases, threat actors even recommend physically maintaining abandoned properties to make them appear occupied, reducing the risk of drawing attention while using the address for fraudulent purposes.
New fraud tutorials are spreading across dark web forums and Telegram.
Threat actors share fraud playbooks, stolen credentials, and fake document services across dark web forums and Telegram channels.
Flare monitors these sources continuously, so you can detect exposure before it enables account takeovers, mail fraud, or identity theft.
Monitoring incoming mail to identify valuable targets
Once a suitable address is identified, the next phase involves utilizing legitimate digitalized postal services for discovery and monitoring of incoming mail.
Informed Delivery, for instance, is a free service that provides residential consumers with digital previews of their incoming letter-sized mail and tracks package deliveries.
By registering these services for the selected address, attackers can monitor incoming correspondence remotely, allowing them to identify valuable items such as financial documents, credit cards, or verification letters before physically accessing the mailbox.
This transforms mail delivery into a form of intelligence gathering, enabling more targeted and efficient fraud.
If the address is already registered, the tutorial references change-of-address requests as a way to regain control over mail delivery. These services are designed for legitimate users relocating their residence and are widely available through postal systems such as USPS.
For example, users can submit a permanent or a temporary Change of Address (COA) request online or in person, enabling mail to be forwarded to a new location for periods ranging from several weeks up to 12 months.
Additional services, such as Premium Forwarding, can consolidate and redirect all incoming mail on a recurring basis.
While these mechanisms include identity verification safeguards such as requiring a small online payment tied to a billing address or presenting a valid photo ID in person, the tutorial suggests that actors perceive these controls as potentially insufficient or inconsistently enforced.
In particular, the ability to submit forwarding requests remotely, combined with the reliance on address-linked verification rather than strong identity binding, may create opportunities for abuse if supporting identity information is compromised or fabricated.
As a result, control over mail delivery may, in some cases, be reassigned without direct interaction with the legitimate resident, turning a service intended for convenience into a potential vector for unauthorized redirection.
At this stage, the operation moves beyond passive targeting and into active monitoring, providing attackers with visibility that significantly increases the success rate of downstream fraud.
Establishing persistence through mail forwarding
After confirming that valuable mail is being delivered, the workflow shifts toward establishing long-term access through mail forwarding services.
Actors are instructed to create personal mailbox accounts that allow them to redirect all incoming mail from the drop address to a separate location under their control.
Because these services typically require identity verification, attackers rely on fake identities, forged documents, or purchased personal data to complete the process.
This marks a critical transition from opportunistic interception to persistent access. Once mail forwarding is in place, attackers no longer need to revisit the physical location, reducing exposure while maintaining continuous access to sensitive information.
The use of fake identities, often involving fabricated personal details or Credit Privacy Numbers (CPNs), demonstrates how this technique integrates with broader fraud ecosystems.
Rather than operating in isolation, drop address abuse becomes one component in a larger pipeline that can support account takeovers, credit fraud, and refund scams.
In practice, these fake identities can be used to register mailbox services, submit forwarding requests, or receive sensitive financial correspondence tied to victim accounts.
This allows actors to bridge the gap between digital compromise and real-world access, enabling them to complete verification steps, intercept authentication materials, or establish new accounts under assumed identities.
As a result, control over a physical address can become an important step in fraud operations that depend on both identity credibility and access to legitimate communication channels.
A hybrid fraud model blending digital and physical layers
The method outlined in the tutorial reflects a broader evolution in fraud operations, where digital intelligence gathering is combined with physical-world manipulation.
In addition to leveraging online platforms and postal services, actors also describe using individuals (sometimes recruited from vulnerable populations) to physically access mailboxes or collect delivered items.
This introduces a human layer into the operation, allowing attackers to outsource risk and further distance themselves from direct involvement.
The activity described in the tutorial reflects a broader rise in mail-enabled fraud documented in recent reporting. According to U.S. Postal Inspection Service–related data, reports of mail theft have increased significantly in recent years, with theft from mail receptacles rising by 139% between 2019 and 2023.
Financially, the impact is substantial, with mail theft schemes linked to hundreds of millions of dollars in suspicious activity tied to check fraud.
At the same time, abuse of postal redirection services, similar to the technique referenced in the tutorial, has also grown, with change-of-address fraud increasing sharply year-over-year. Together, these trends highlight how control over physical mail has become valuable.
At the same time, the tutorial acknowledges operational challenges. Virtual addresses and commonly reused locations are increasingly flagged by financial institutions, suggesting that defenders are beginning to incorporate address-based risk signals into their detection models.
As a result, actors emphasize the importance of finding “clean” residential addresses that have not yet been associated with fraudulent activity.
Together, these elements illustrate a fraud model that is not driven by technical sophistication, but by coordination, adaptability, and the strategic use of legitimate systems.
Not an Isolated Tutorial / Fraud
While this may look like an isolated tutorial, this is part of a broader phenomenon or tutorials on how to find physical drop address, some are for free and others are paid for.
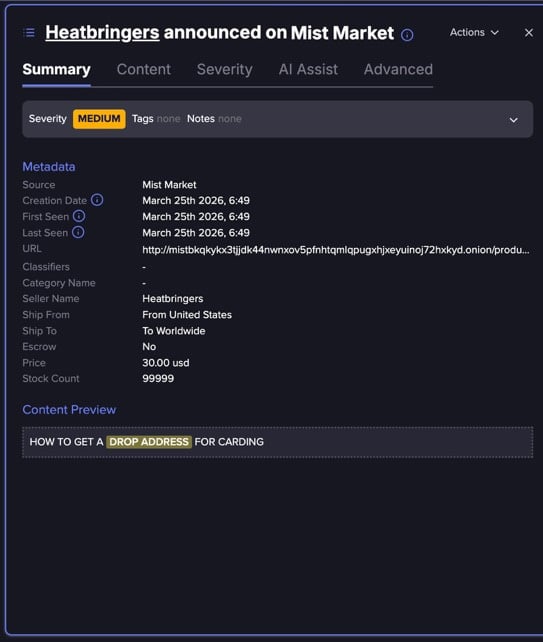
Flare link to post, sign up for the free trial to access if you aren’t already a customer.
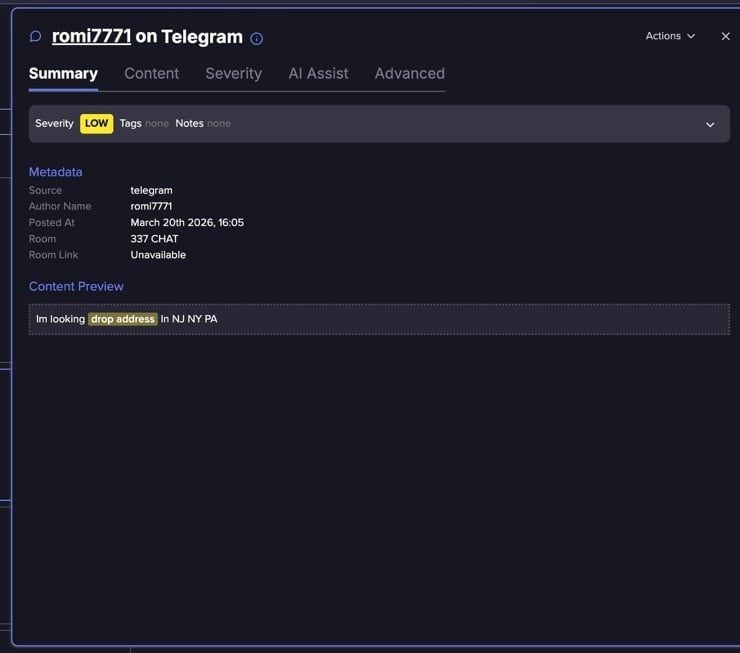
Flare link to post, sign up for the free trial to access if you aren’t already a customer.
Expanding attack surface beyond traditional cybersecurity controls
The emergence of these techniques underscores a growing challenge for organizations: many of the systems being abused: real estate platforms, postal services, and identity verification processes, exist outside the scope of traditional cybersecurity defenses.
As fraud operations continue to evolve, detection increasingly depends on correlating signals across domains, including address usage patterns, mail forwarding activity, and identity inconsistencies. Without this broader visibility, attacks that rely on legitimate services rather than technical exploits may continue to evade conventional security controls.
Learn more by signing up for our free trial.
Sponsored and written by Flare.