
Hackers have targeted TrueConf conference servers in attacks that exploit a zero-day vulnerability, allowing them to execute arbitrary files on all connected endpoints.
The flaw is tracked as CVE-2026-3502 and received a medium severity score. It stems from a missing integrity check in the software’s update mechanism, which can be used to replace the legitimate update with a malicious variant.
TrueConf is a video conferencing platform that can run as a self-hosted server. Although it also supports cloud deployments, it is generally designed for closed, offline environments.
According to the vendor, more than 100,000 organizations transitioned to TrueConf during the COVID-19 pandemic for remote online business activities. Among TrueConf users are military forces, government agencies, oil and gas corporations, and air traffic management companies.
CheckPoint researchers have been tracking a campaign they track as TrueChaos that, since the beginning of the year, has exploited CVE-2026-3502 in zero-day attacks targeting government entities in Southeast Asia.
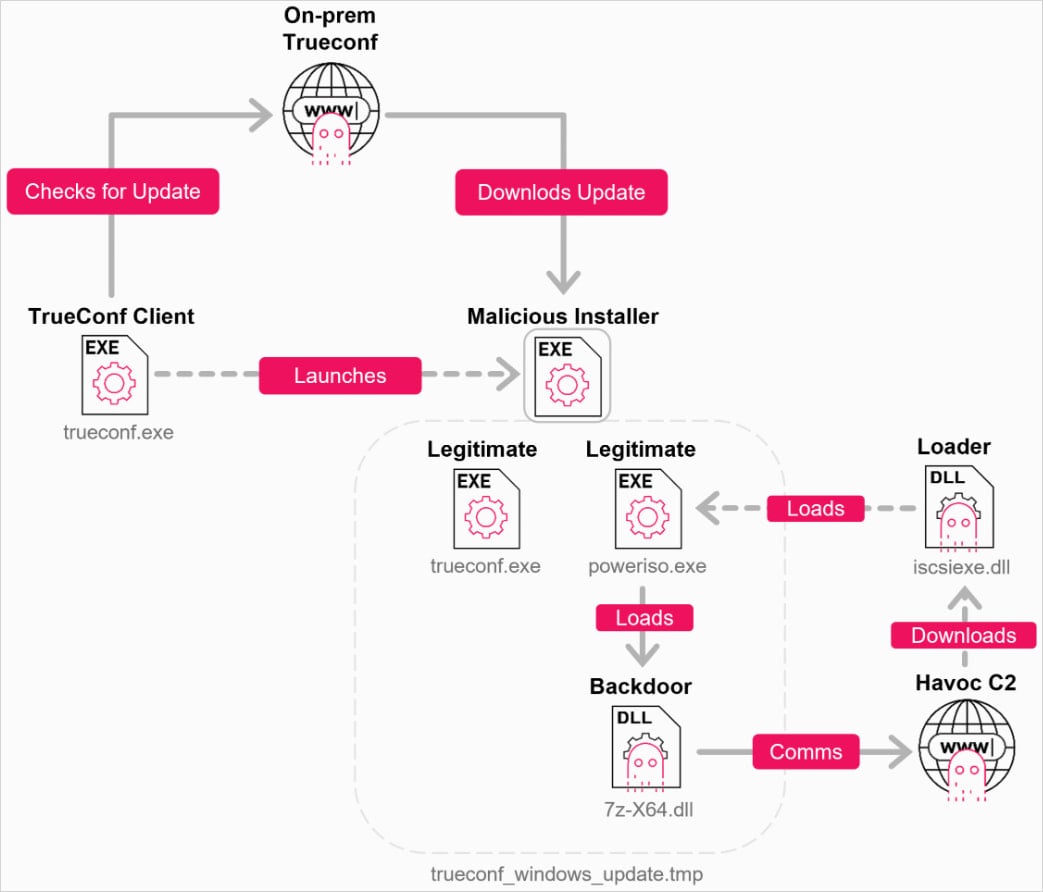
“An attacker who gains control of the on-premises TrueConf server can replace the expected update package with an arbitrary executable, presented as the current application version, and distribute it to all connected clients,” CheckPoint says.
“Because the client trusts the server-provided update without proper validation, the malicious file can be delivered and executed under the guise of a legitimate TrueConf update.”
The flaw affects TrueConf versions 8.1.0 through 8.5.2, and following CheckPoint’s report to the vendor, a fix was released in version 8.5.3 in March 2026.
“TrueChaos” operation
CheckPoint has moderate confidence in attributing the TrueChaos activity to a Chinese-nexus threat actor, based on tactics, techniques, and procedures (TTPs), the use of Alibaba Cloud and Tencent for hosting the command and control (C2) infrastructure, and victimology.
The attacks spread through a centrally managed government TrueConf server, impacting multiple agencies, pushing malicious files via fake updates to all connected TrueConf clients.
Source: Check Point
The infection chain includes DLL sideloading and the deployment of reconnaissance tools (tasklist, tracert), privilege escalation (UAC bypass via iscicpl.exe), and the establishment of persistence.
The researchers were unable to recover the final payload, but noted that network traffic pointed to Havoc C2 infrastructure, making it highly likely that the Havoc implant was used.
Source: Check Point
Havoc is an open-source C2 framework capable of executing commands, managing processes, manipulating Windows tokens, executing shellcode, and deploying additional payloads on compromised systems.
It has previously been used by the Chinese threat cluster ‘Amaranth Dragon’ in attacks with a similar targeting scope.
CheckPoint’s report shares indicators of compromise (IoCs) as well as multiple infection signals. Strong signs of a breach include the presence of poweriso.exe or 7z-x64.dll, and suspicious artifacts like %AppData%RoamingAdobeupdate.7z or iscsiexe.dll.
Automated Pentesting Covers Only 1 of 6 Surfaces.
Automated pentesting proves the path exists. BAS proves whether your controls stop it. Most teams run one without the other.
This whitepaper maps six validation surfaces, shows where coverage ends, and provides practitioners with three diagnostic questions for any tool evaluation.
Related Articles:
Ransomware gang exploits Cisco flaw in zero-day attacks since January
Google says 90 zero-days were exploited in attacks last year
Android gets patches for Qualcomm zero-day exploited in attacks
Critical Cisco SD-WAN bug exploited in zero-day attacks since 2023
CISA orders feds to patch actively exploited Dell flaw within 3 days
