
The Federal Police in Germany (BKA) has identified two Russian nationals as the leaders of GandCrab and REvil ransomware operations between 2019 and 2021.
According to BKA’s disclosure, 31-year-old Daniil Maksimovich Shchukin and 43-year-old Anatoly Sergeevitsch Kravchuk acted as the heads of the two ransomware groups “from at least the beginning of 2019 until at least July 2021.”
Shchukin hid behind the monikers UNKN/UNKNOWN for years, posting on cybercrime forums and speaking as a representative of the ransomware operation.
The German authorities say that Shchukin and Kravchuk participated in at least 130 extortion cases targeting companies in the country specifically.
Following these attacks, at least 25 victims paid Shchukin and his co-conspirators $2.2 million in ransom, while the total financial damage caused by them is estimated in excess of $40 million.
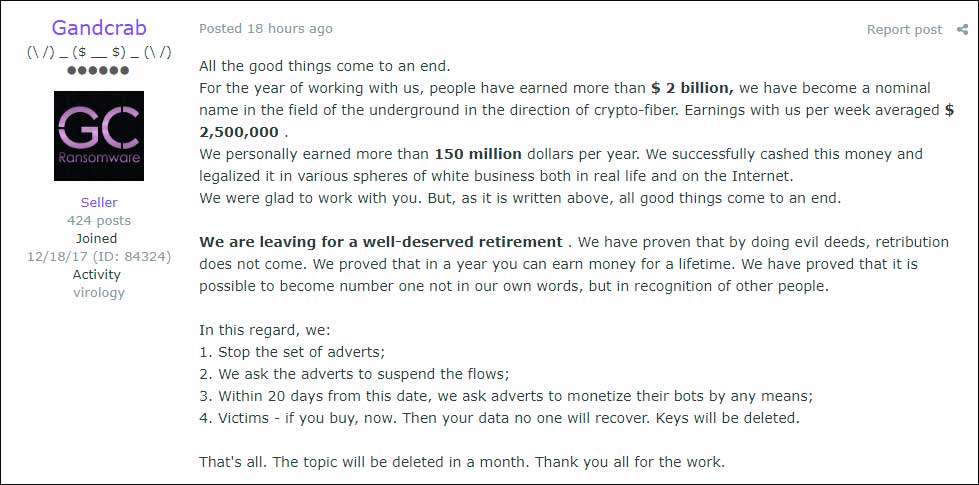
GandCrab started in early 2018, and its leader at the time decided to retire in June 2019, after claiming to have earned $2 billion from ransom payments. The leader, however, cashed out with $150 million, which they claimed to have invested in legal businesses.
source: BleepingComputer
Soon after, a new operation called REvil emerged, following the affiliate model established by GandCrab through advertising and building partnerships with cybercriminals.
REvil, also known as Sodinokibi, was formed from previous GandCrab affiliates and operators who had already learned the successful tactics and started to apply them to their operations.
REvil later added public leak sites and ran data auctions to pressure victims. Notable victims include multiple Texas local governments, computer giant Acer, and the Kaseya supply-chain attack that impacted around 1,500 downstream victims.
Following the massive Kaseya hack, REvil took a two-month break, during which law enforcement breached their servers and started to monitor operations.
Multiple infrastructure disruptions were recorded at the time, and in mid-January 2022, Russia arrested more than a dozen REvil gang members, who were released in 2025 after time served on carding charges.
It is unclear if either Shchukin or Kravchuk joined other ransomware operations following REvil’s demise in 2021.
BKA believes that Shchukin and Kravchuk are now in Russia and asks the public to share any information that could lead to their whereabouts. Relevant entries were also created on the EU’s Most Wanted portal.
The police shared several images, including tattoo photos, to help track down the two threat actors and bring them to justice.
Automated Pentesting Covers Only 1 of 6 Surfaces.
Automated pentesting proves the path exists. BAS proves whether your controls stop it. Most teams run one without the other.
This whitepaper maps six validation surfaces, shows where coverage ends, and provides practitioners with three diagnostic questions for any tool evaluation.
Related Articles:
Interpol operation Synergia takes down 1,300 servers used for cybercrime
Police arrests 2 Phobos ransomware suspects, seizes 8Base sites
GandCrab Ransomware Shutting Down After Claiming to Earn $2 Billion
Die Linke German political party confirms data stolen by Qilin ransomware
Manager of botnet used in ransomware attacks gets 2 years in prison

