
A new campaign delivering the Atomic Stealer malware to macOS users abuses the Script Editor in a variation of the ClickFix attack that tricked users into executing commands in Terminal.
Script Editor is a built-in macOS application for writing and running scripts, primarily AppleScript and JXA, that can execute local scripts and shell commands. It is a trusted application pre-installed on macOS systems.
While this is not the first time it has been abused for malware delivery, the researchers note that, in the context of the ClickFix social engineering technique, it does not require the victim to manually interact with the Terminal and execute commands.
Apart from the Terminal-based variant being widely reported, macOS Tahoe 26.4 added protection against ClickFix attacks in the form of a warning when trying to execute commands.
In a new campaign distributing Atomic Stealer observed by security researchers at Jamf, the hackers target victims with fake Apple-themed sites that pose as guides to help reclaim disk space on their Mac computers.
These pages contain legitimate-looking system cleanup instructions but use the applescript:// URL scheme to launch Script Editor with a pre-filled executable code.
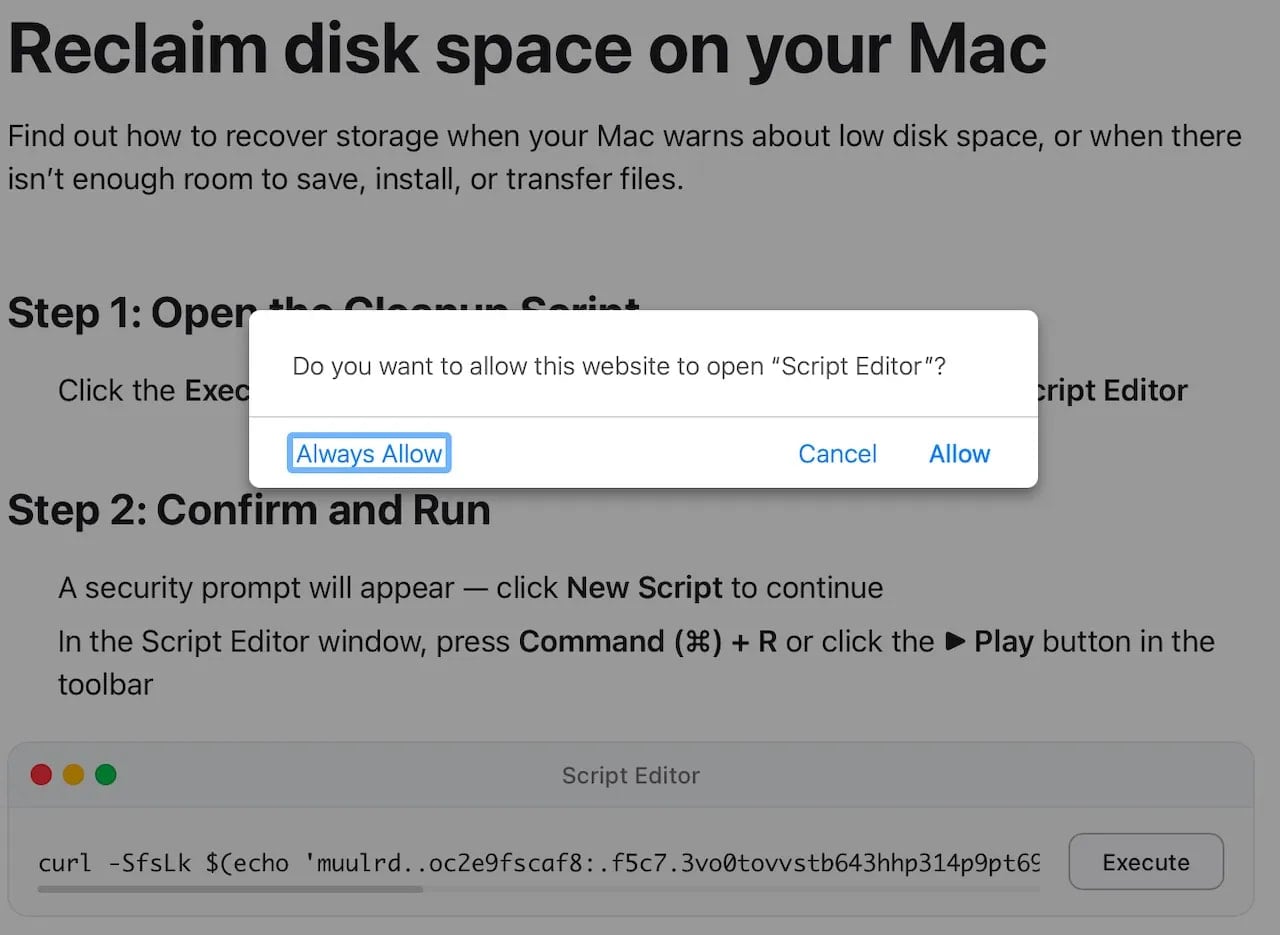
Source: Jamf
The malicious code runs an obfuscated ‘curl | zsh’ command, which downloads and executes a script directly in system memory.
This decodes a base64 + gzip payload, downloads a binary (/tmp/helper), removes security attributes via ‘xattr -c,’ makes it executable, and runs it.
The final payload is a Mach-O binary identified as Atomic Stealer (AMOS), a commodity malware-as-a-service that has been extensively deployed in ClickFix campaigns using various lures over the past year.
The malware targets a broad spectrum of sensitive data, including information stored in the Keychain, desktop, and browser cryptocurrency wallet extensions, browser autofill data, passwords, cookies, stored credit cards, and system information.
Last year, AMOS also added a backdoor component to give operators persistent access to compromised systems.
Mac users should treat Script Editor prompts as high-risk and avoid running them on their devices unless they fully understand what they do and trust the resource.
For macOS troubleshooting guides, it is recommended to rely only on official documentation from Apple.
Apple Support Communities, the forum where Apple customers can help each other with advice, although it may not be risk-free.
Automated Pentesting Covers Only 1 of 6 Surfaces.
Automated pentesting proves the path exists. BAS proves whether your controls stop it. Most teams run one without the other.
This whitepaper maps six validation surfaces, shows where coverage ends, and provides practitioners with three diagnostic questions for any tool evaluation.
Related Articles:
New Infinity Stealer malware grabs macOS data via ClickFix lures
Bing AI promoted fake OpenClaw GitHub repo pushing info-stealing malware
Apple adds macOS Terminal warning to block ClickFix attacks
Suspected RedLine infostealer malware admin extradited to US
New Torg Grabber infostealer malware targets 728 crypto wallets

