A new report from Infoblox Threat Intel connects two issues that are often discussed separately but rarely proven to be linked. The company says it has identified the first confirmed relationship between a Southeast Asian scam compound built on forced labour and an Android banking trojan used in attacks across 21 countries.
The research, conducted with Vietnamese non-profit Chong Lua Dao, shows how people trafficked into scam centres are forced to support a malware distribution system that targets mobile banking users. According to researchers, this connection shows how people are being forced to help run scams that steal from others online.
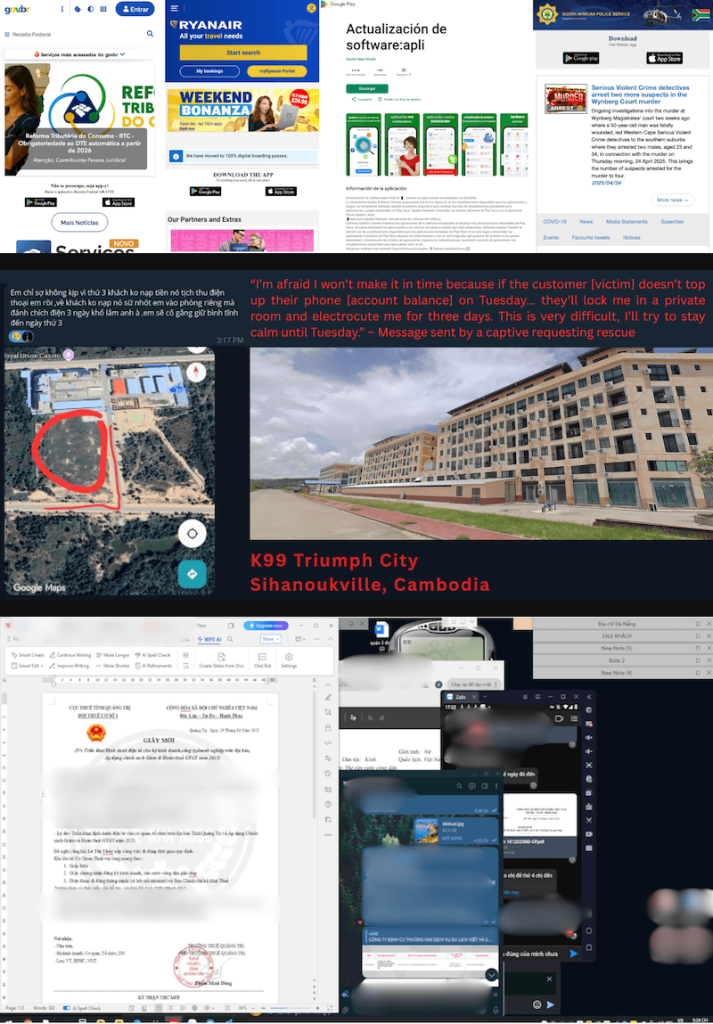
Looking at how the malware spreads, the report points to fake domains being created month after month. Investigators tracked roughly 35 new domains being registered regularly, all designed to mimic trusted services or banking interfaces.
These sites trick victims into installing malicious Android apps disguised as legitimate tools. The report describes common lures such as fake banking alerts, delivery notifications, or messages that push users to install an app outside official app stores.
Once installed, the trojan gives attackers a high level of control over the device. It can intercept SMS messages, bypass biometric checks, and manipulate banking sessions in real time. That combination allows attackers to move funds without any alert that users expect to protect them.
According to Infoblox’s report shared with Hackread.com, victims have been identified in multiple parts of the world, including Indonesia and Thailand in Southeast Asia, Spain and Türkiye in Europe, and several countries in Latin America. This points to an infrastructure that can target different banks and adjust to local languages, which helps improve its success rate.
Malware-As-A-Service
Researchers have described the operation as malware-as-a-service, where the tools and infrastructure are maintained centrally while affiliates handle distribution and victim engagement. That setup makes it easier for more groups to get involved without having to build anything themselves.
Another detail highlighted in the research is how the malware keeps control even after installation. It can overlay fake login screens on top of real banking apps, capture credentials as they are entered, and forward that data to attackers. In some cases, it can also take control of the device remotely, allowing attackers to carry out transactions as if they were the user.
K99 Triumph City, Cambodia, Slavery and Scams
Researchers noted the malware operation is being hosted from several locations, including the K99 Triumph City compound, reportedly, a heavily fortified cybercrime compound located in Sihanoukville, Cambodia.
The connection to scam compounds in Cambodia makes the situation more serious. Infoblox Threat Intel and Chong Lua Dao say individuals inside these facilities are forced to manage parts of the operation, from sending phishing messages to guiding victims through the installation process. This turns what might look like a standard cybercrime campaign into a system built on organised crime and active slavery.
These findings carry weight. As reported by Hackread.com in April 2024, Indian law enforcement agencies rescued hundreds of their citizens who had been lured to Cambodia with false promises of legitimate jobs, only to be forced to work for cybercrime gangs.
If you are offered a job in Cambodia, the risks should not be ignored. If you use an Android device, stick to official app stores and avoid downloading unnecessary apps. For a deeper look at this threat, Infoblox’s report includes detailed technical insights, including IOCs.