
Education company McGraw-Hill has confirmed in a statement to BleepingComputer that hackers exploited a Salesforce misconfiguration and accessed its internal data.
The company assured that the breach did not affect its Salesforce accounts, customer databases, or internal systems, and that the amount of exposed data is limited and non-sensitive.
“McGraw-Hill recently identified unauthorized access to a limited set of data from a webpage hosted by Salesforce on its platform. This activity appears to be part of a broader issue involving a misconfiguration within Salesforce’s environment that has impacted multiple organizations that work with Salesforce,” a McGraw-Hill spokesperson told BleepingComputer.
“Importantly, this did not involve unauthorized access to McGraw-Hill’s Salesforce accounts, customer databases, courseware, or internal systems,” the company representative added.
McGraw-Hill further states that its investigation, with help from external cybersecurity experts, revealed that the exposed information does not contain Social Security numbers (SSNs), financial account information, or student data from its educational platforms.
A global education company focused on learning content and platforms, McGraw-Hill offers textbooks, digital learning platforms, and K-12 school and university systems. The company is a major player in education publishing, with an annual revenue of $2.2 billion.
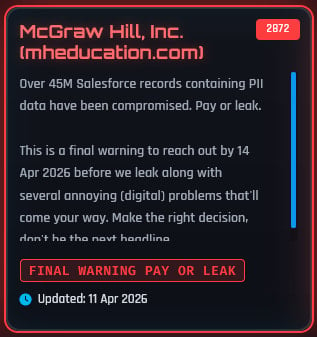
The statement about the cyberattack comes in response to the extortion group ShinyHunters announcing McGraw-Hill as a victim on its dark-web portal and threatening to leak stolen data by April 14 unless a ransom is paid.
The notorious threat actor claims to hold 45 million Salesforce records containing personally identifiable information (PII), contradicting the company’s statement that the compromised data is not sensitive in nature.
Source: BleepingComputer
McGraw-Hill also told BleepingComputer that the affected webpages were secured immediately after detecting the unauthorized activity, and that it is working closely with Salesforce to further strengthen protections and ensure that the issue is fully addressed.
The ShinyHunters data extortion group has carried out several confirmed high-profile security breaches since the start of the year, including those against Rockstar Games, Hims & Hers, the European Commission, Telus Digital, Wynn Resorts, Canada Goose, Match Group, Panera Bread, and CarGurus.
In March, the threat group also breached the American firm Infinite Campus, which also operates a K-12 student information system.
Automated Pentesting Covers Only 1 of 6 Surfaces.
Automated pentesting proves the path exists. BAS proves whether your controls stop it. Most teams run one without the other.
This whitepaper maps six validation surfaces, shows where coverage ends, and provides practitioners with three diagnostic questions for any tool evaluation.
Related Articles:
Infinite Campus warns of breach after ShinyHunters claims data theft
European Commission confirms data breach after Europa.eu hack
ShinyHunters launches Salesforce data leak site to extort 39 victims
Stolen Rockstar Games analytics data leaked by extortion gang
Snowflake customers hit in data theft attacks after SaaS integrator breach

