
A researcher known as “Chaotic Eclipse” has published a proof-of-concept exploit for a second Microsoft Defender zero-day, dubbed “RedSun,” in the past two weeks, protesting how the company works with cybersecurity researchers.
This exploit is for a local privilege escalation (LPE) flaw that grants SYSTEM privileges in Windows 10, Windows 11, and Windows Server on the latest April Patch Tuesday patches, when Windows Defender is enabled.
“When Windows Defender realizes that a malicious file has a cloud tag, for whatever stupid and hilarious reason, the antivirus that’s supposed to protect decides that it is a good idea to just rewrite the file it found again to it’s original location,” explains the researcher.
“The PoC abuses this behaviour to overwrite system files and gain administrative privileges.”
Will Dormann, principal vulnerability analyst at Tharros, has confirmed to BleepingComputer that the exploit for the new Microsoft Defender RedSun zero-day works and grants SYSTEM privileges on fully patched Windows 10, Windows 11, and Windows Server 2019 and later.
“This Exploit uses the ‘Cloud Files API’, writes EICAR to a file using it, uses an oplock to win a volume shadow copy race, and uses a directory junction/reparse point to redirect the file rewrite (with new contents) to C:Windowssystem32TieringEngineService.exe,” Dormann wrote in a thread on Mastodon.
“At this point, the Cloud Files Infrastructure runs the attacker-planted TieringEngineService.exe (which is the RedSun.exe exploit itself) as SYSTEM. Game over.”
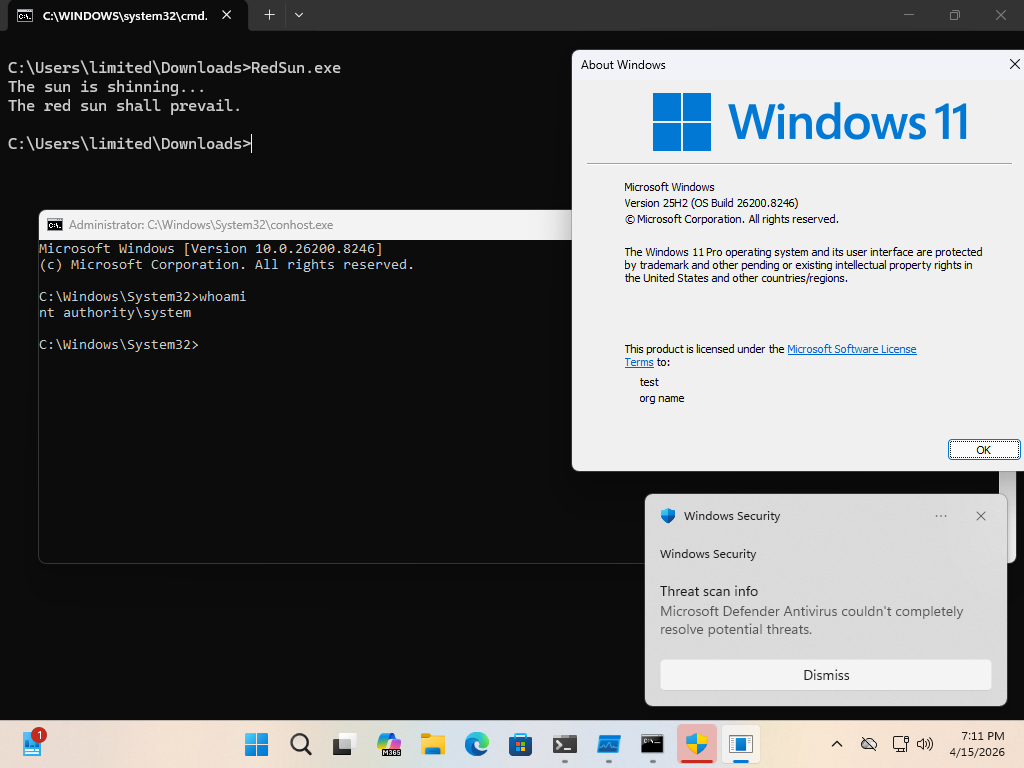
Source: Dormann
Dormann says that some antivirus vendors on VirusTotal are detecting the exploit [VirusTotal] because the exploit executable contains an embedded EIRCAR (antivirus test file). However, he reduced detections [VirusTotal] by encrypting the EICAR string within the executable.
Last week, this researcher, known as “Chaotic Eclipse,” released an exploit for a different Microsoft Defender LPE zero-day, dubbed “BlueHammer,” which is now tracked as CVE-2026-33825. Microsoft fixed the flaw as part of this month’s Patch Tuesday security updates.
The researcher says they published both zero-day PoCs in protest at how Microsoft works with cybersecurity researchers who disclose vulnerabilities to the Microsoft Security Response Center (MSRC).
“Normally, I would go through the process of begging them to fix a bug but to summarize, I was told personally by them that they will ruin my life and they did and I’m not sure if I was the only who had this horride experience or few people did but I think most would just eat it and cut their losses but for me, they took away everything,” alleged the researcher.
“They mopped the floor with me and pulled every childish game they could. It was soo bad at some point I was wondering if I was dealing with a massive corporation or someone who is just having fun seeing me suffer but it seems to be a collective decision.”
BleepingComputer contacted the researcher for more details on their interaction with the MSRC.
When contacting Microsoft about these alleged issues, they shared the following statement.
“Microsoft has a customer commitment to investigate reported security issues and update impacted devices to protect customers as soon as possible,” a Microsoft spokesperson told BleepingComputer.
“We also support coordinated vulnerability disclosure, a widely adopted industry practice that helps ensure issues are carefully investigated and addressed before public disclosure, supporting both customer protection and the security research community.”
Automated Pentesting Covers Only 1 of 6 Surfaces.
Automated pentesting proves the path exists. BAS proves whether your controls stop it. Most teams run one without the other.
This whitepaper maps six validation surfaces, shows where coverage ends, and provides practitioners with three diagnostic questions for any tool evaluation.
Related Articles:
Microsoft: April updates trigger BitLocker key prompts on some servers
Microsoft adds Windows protections for malicious Remote Desktop files
Hackers exploiting Acrobat Reader zero-day flaw since December
Disgruntled researcher leaks “BlueHammer” Windows zero-day exploit
Ex-L3Harris exec jailed for selling zero-days to Russian exploit broker

