
The Payouts King ransomware is using the QEMU emulator as a reverse SSH backdoor to run hidden virtual machines on compromised systems and bypass endpoint security.
QEMU is an open-source CPU emulator and system virtualization tool that allows users to run operating systems on a host computer as virtual machines (VMs).
Since security solutions on the host cannot scan inside the VMs, attackers can use them to execute payloads, store malicious files, and create covert remote access tunnels over SSH.
For these reasons, QEMU has been abused in past operations from multiple threat actors, including the 3AM ransomware group, LoudMiner cryptomining, and ‘CRON#TRAP’ phishing.
Researchers at cybersecurity company Sophos documented two campaigns where attackers deployed QEMU as part of their arsenal and to collect domain credentials.
One campaign that Sophos tracks as STAC4713 was first observed in November 2025 and has been linked to the Payouts King ransomware operation.
The other, tracked as STAC3725, has been spotted in February this year and exploits the CitrixBleed 2 (CVE‑2025‑5777) vulnerability in NetScaler ADC and Gateway instances.
Running Alpine Linux VMs
Researchers note that the threat actors behind the STAC4713 campaign are associated with the GOLD ENCOUNTER threat group, which is known to target hypervisors and encryptors for VMware and ESXi environments.
According to Sophos, the malicious actor creates a scheduled task named ‘TPMProfiler’ to launch a hidden QEMU VM as SYSTEM.
They use virtual disk files disguised as databases and DLL files, and set up port forwarding to provide covert access to the infected host via a reverse SSH tunnel.
The VM runs Alpine Linux version 3.22.0 that includes attacker tools such as AdaptixC2, Chisel, BusyBox, and Rclone.
Sophos notes that initial access was achieved via exposed SonicWall VPNs, while exploitation of the SolarWinds Web Help Desk vulnerability CVE-2025-26399 was observed in more recent attacks.
In the post-infection phase, the threat actors used VSS (vssuirun.exe) to create a shadow copy, then used the print command over SMB to copy NTDS.dit, SAM, and SYSTEM hives to temp directories.
More recently observed incidents attributed to the threat actor relied on other initial access vectors. The researchers say that in an attack in February, GOLD ENCOUNTER used an exposed Cisco SSL VPN, and in March they posed as IT staff and tricked employees over Microsoft Teams into downloading and installing QuickAssist.
“In both instances, the threat actors used the legitimate ADNotificationManager.exe binary to sideload a Havoc C2 payload (vcruntime140_1.dll) and then leveraged Rclone to exfiltrate data to a remote SFTP location” – Sophos
According to a Zscaler report this week, Payouts King is likely tied to former BlackBasta affiliates, based on its use of similar initial access methods like spam bombing, Microsoft Teams phishing, and Quick Assist abuse.
The strain employs heavy obfuscation and anti-analysis mechanisms, establishes persistence via scheduled tasks, and terminates security tools using low-level system calls.
Payouts King encryption scheme uses AES-256 (CTR) with RSA-4096 with intermittent encryption for larger files. The dropped ransom notes point victims to leak sites on the dark web.
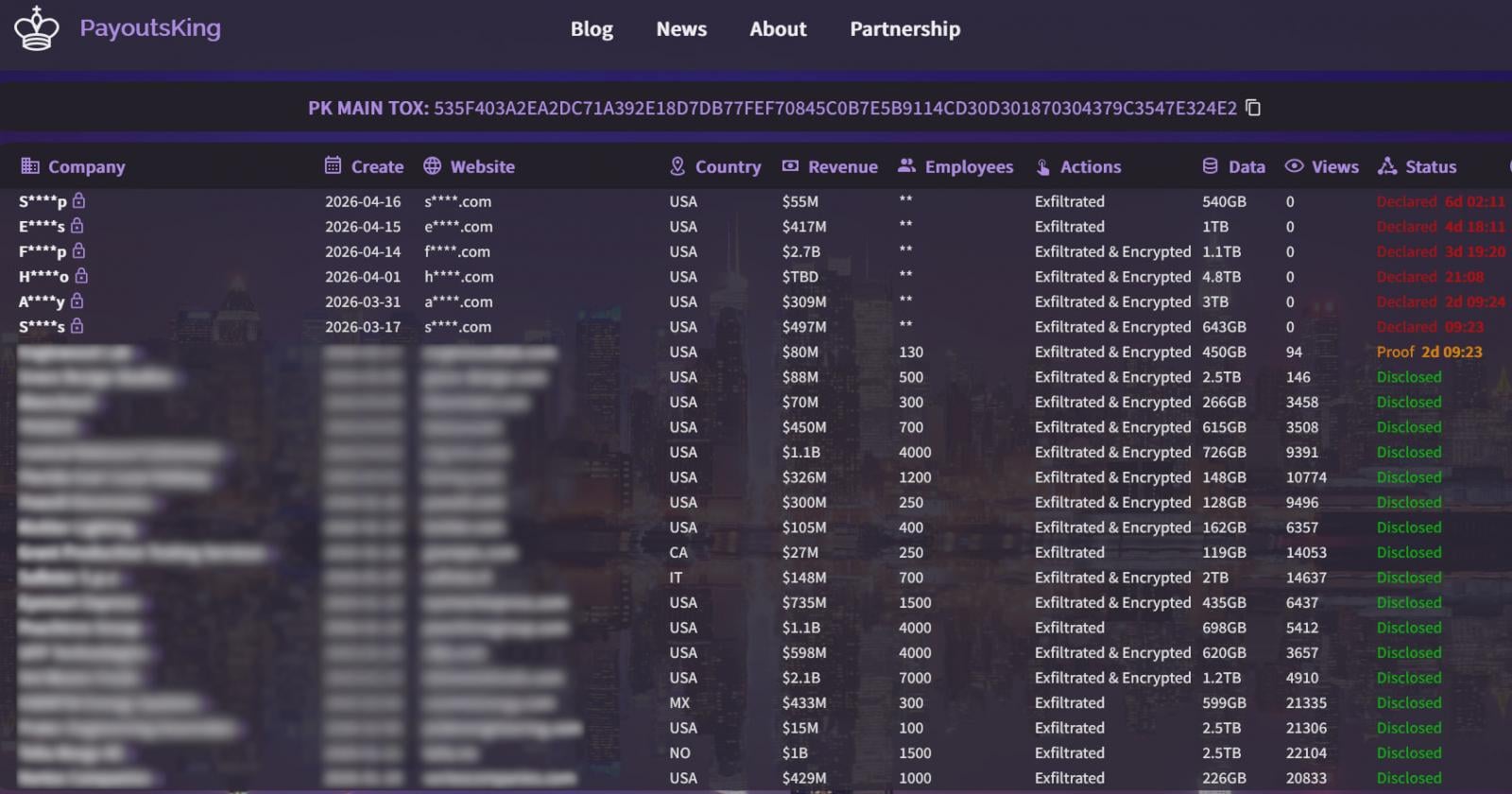
Source: BleepingComputer
The second campaign that Sophos observed (STAC3725), has been active since February and exploits the CitrixBleed 2 vulnerability to gain initial access to target environments.
After compromising NetScaler devices, the attackers deploy a ZIP archive containing a malicious executable that installs a service named ‘AppMgmt,’ creates a new local admin user (CtxAppVCOMService), and installs a ScreenConnect client for persistence.
The ScreenConnect client connects to a remote relay server and establishes a session with system privileges, then drops and extracts a QEMU package that runs a hidden Alpine Linux VM using a custom.qcow2 disk image.
Instead of using a pre-built toolkit, the attackers manually install and compile their tools, including Impacket, KrbRelayx, Coercer, BloodHound.py, NetExec, Kerbrute, and Metasploit, inside the VM.
Observed activity includes credential harvesting, Kerberos username enumeration, Active Directory reconnaissance, and staging data for exfiltration via FTP servers.
Sophos recommends that organizations look for unauthorized QEMU installations, suspicious scheduled tasks running with SYSTEM privileges, unusual SSH port forwarding, and outbound SSH tunnels on non-standard ports.
99% of What Mythos Found Is Still Unpatched.
AI chained four zero-days into one exploit that bypassed both renderer and OS sandboxes. A wave of new exploits is coming.
At the Autonomous Validation Summit (May 12 & 14), see how autonomous, context-rich validation finds what’s exploitable, proves controls hold, and closes the remediation loop.
Related Articles:
LeakNet ransomware uses ClickFix, Deno runtime in stealthy attacks
Signed software abused to deploy antivirus-killing scripts
Healthcare IT solutions provider ChipSoft hit by ransomware attack
Microsoft links Medusa ransomware affiliate to zero-day attacks
German authorities identify REvil and GandCrab ransomware bosses

